WXID怎么转换成手机号 |
您所在的位置:网站首页 › wxid_1ixr45bdfp7l21微信号怎么添加 › WXID怎么转换成手机号 |
WXID怎么转换成手机号
|
之前有朋友问过我类似的问题,他说在项目上有这么个需求,需要把原始wxid绑定的手机号查出来。也是出于人情世故,帮他研究了一段时间,在这期间我分析了wxid的构成,但是没有什么大的突破,后面分析了一下微信的相关接口,发现有一个接口是能够将原始id的手机号给拿到的。 发现了之后马上就写这篇博客了。 以下内容仅提供大家学习。 前面利用OD工具分析了微信的十几个18年19年的版本,分析到7.0.5版本的时候发现微信有一个隐藏的接口,列出了以下步骤 本文仅限学习交流,请勿用于非法以及商业用途,由于时间和水平有限,文中错漏之处在所难免,请多多批评指正。 一、产品基本介绍产品应用场景主要用于营销活动反作弊、渠道推广反作弊、交易安全保护、账户安全保护、接口安全保护。渠道买量、应用推广、小程序推广。 产品功能: 虚假行为分析 从设备与账户维度进行聚类关联分析、行为异常分析,甄别虚假作弊用户、IP、设备,锁定源头风险。 终端风险感知 有效识别模拟器、群控、作弊设备、模拟器、农场工具。 大数据关联分析 结合渠道大数据与风险数据,筛选出可疑对象和目标,通过特定业务判断完成风险环形数据的合围,支持算法模型的嵌入。 二、产品整体框架2.1、产品使用步骤 2.1.1. 前端接入:根据前端类型选择对应 SDK 进行接入,支持 Android App、iOS iApp、小程 序(头条小程序、微信小程序、支付宝小程序)、WEB/WAP/H5。 2.1.2. 接入验证:前后端接入完成后,联合客户端、服务端进行整体联调。 2.1.3. 运行APP成功返回blackbox设备指纹。 2.2、整体对接数据流程时序图
2.3、产品整体架构 接入产品逆向分析还原出基本的产品架构,如图2-3所示
三、JAVA与JNI初始化 3.1、在应用启动的时候,比如在应用的首页 Activity 的 onCreate 方法中调用以下方法: 复制代码 隐藏代码 // FMAgent.ENV_SANDBOX 表示沙盒环境 // FMAgent.ENV_PRODUCTION 表示生产环境 FMAgent.initWithCallback(this, FMAgent.ENV_PRODUCTION, new FMCallback() { @Override public void onEvent(String s) { tdBlackbox = s; Log.e(TAG,"blackbox:"+tdBlackbox); runOnUiThread(new Runnable() { @Override public void run() { tv1.setText("blackbox内容是:"+tdBlackbox); } }); } });3.2、加载SO 复制代码 隐藏代码 JSONObject v6 = null; try { if(Build.VERSION.SDK_INT >= 17) { System.loadLibrary("tdvm"); } System.loadLibrary("tongdun"); goto label_405; } catch(Throwable v6_1) { }3.3、执行NI_OnLoad注册Native方法 复制代码 隐藏代码 .text:000000709EAE5E4C RegisterNatives_sub_786D163E4C .text:000000709EAE5E4C .text:000000709EAE5E4C var_38= -0x38 .text:000000709EAE5E4C var_2C= -0x2C .text:000000709EAE5E4C var_28= -0x28 .text:000000709EAE5E4C var_20= -0x20 .text:000000709EAE5E4C var_18= -0x18 .text:000000709EAE5E4C var_10= -0x10 .text:000000709EAE5E4C .text:000000709EAE5E4C ; __unwind { // 1000 .text:000000709EAE5E4C FF 03 01 D1 SUB SP, SP, #0x40 .text:000000709EAE5E50 FE 1B 00 F9 STR X30, [SP,#0x40+var_10] .text:000000709EAE5E54 E1 17 00 F9 STR X1, [SP,#0x40+var_18] .text:000000709EAE5E58 E2 13 00 F9 STR X2, [SP,#0x40+var_20] .text:000000709EAE5E5C E3 0F 00 F9 STR X3, [SP,#0x40+var_28] .text:000000709EAE5E60 E4 17 00 B9 STR W4, [SP,#0x40+var_2C] .text:000000709EAE5E64 E1 17 40 F9 LDR X1, [SP,#0x40+var_18] .text:000000709EAE5E68 E2 13 40 F9 LDR X2, [SP,#0x40+var_20] .text:000000709EAE5E6C E3 0F 40 F9 LDR X3, [SP,#0x40+var_28] .text:000000709EAE5E70 E4 17 40 B9 LDR W4, [SP,#0x40+var_2C] .text:000000709EAE5E74 E0 07 00 F9 STR X0, [SP,#0x40+var_38] .text:000000709EAE5E78 E0 03 01 AA MOV X0, X1 .text:000000709EAE5E7C E1 03 02 AA MOV X1, X2 .text:000000709EAE5E80 E2 03 03 AA MOV X2, X3 .text:000000709EAE5E84 E3 03 04 2A MOV W3, W4 .text:000000709EAE5E88 E8 07 40 F9 LDR X8, [SP,#0x40+var_38] .text:000000709EAE5E8C 00 01 3F D6 BLR X8 ; RegisterNatives .text:000000709EAE5E8C .text:000000709EAE5E90 FE 1B 40 F9 LDR X30, [SP,#0x40+var_10] .text:000000709EAE5E94 FF 03 01 91 ADD SP, SP, #0x40 ; '@' .text:000000709EAE5E98 C0 03 5F D6 RET //native方法 getData2, signature: (Ljava/lang/String;)[B tongdun, signature: (Landroid/content/Context;)V tongdun2, signature: (Landroid/content/Context;)V XOnEvent, signature: (Landroid/content/Context;)Ljava/lang/String; onSensorChanged, signature: (Landroid/hardware/SensorManager;Lcn/tongdun/android/shell/common/s;Landroid/hardware/SensorEvent;)V ##### 3.4、整体流程如图3-4所示 四、VM虚拟机基本逻辑 4.1、VM逻辑主要在模块libtdvm.so中,该模块导出两个方法: 复制代码 隐藏代码 td_eea7e05642c04e240c51 //解压解密VMBycode td_b13d6928ba611f6a6e37 //解析执行VMBycodelibtongdun.so模块中的大部分方法都会调用上面两个方法,传入vmbycode解析执行。 4.2、VM流程与分析思路 td_eea7e05642c04e240c51方法解压解密后VMBycode后进入VM,代码如下: 复制代码 隐藏代码 .text:000000709EA954F0 EnterVM_sub_709EA954F0 .text:000000709EA954F0 .text:000000709EA954F0 var_AC= -0xAC .text:000000709EA954F0 databass= -0xA8 .text:000000709EA954F0 bycode= -0xA0 .text:000000709EA954F0 var_98= -0x98 .text:000000709EA954F0 var_90= -0x90 .text:000000709EA954F0 var_88= -0x88 .text:000000709EA954F0 var_80= -0x80 .text:000000709EA954F0 databass1= -0x78 .text:000000709EA954F0 var_70= -0x70 .text:000000709EA954F0 var_68= -0x68 .text:000000709EA954F0 var_60= -0x60 .text:000000709EA954F0 var_50= -0x50 .text:000000709EA954F0 var_40= -0x40 .text:000000709EA954F0 var_30= -0x30 .text:000000709EA954F0 var_20= -0x20 .text:000000709EA954F0 var_10= -0x10 .text:000000709EA954F0 var_s0= 0 .text:000000709EA954F0 .text:000000709EA954F0 ; __unwind { .text:000000709EA954F0 FF 03 03 D1 SUB SP, SP, #0xC0 .text:000000709EA954F4 E8 2B 00 FD STR D8, [SP,#0xB0+var_60] .text:000000709EA954F8 FC 6F 06 A9 STP X28, X27, [SP,#0xB0+var_50] .text:000000709EA954FC FA 67 07 A9 STP X26, X25, [SP,#0xB0+var_40] .text:000000709EA95500 F8 5F 08 A9 STP X24, X23, [SP,#0xB0+var_30] .text:000000709EA95504 F6 57 09 A9 STP X22, X21, [SP,#0xB0+var_20] .text:000000709EA95508 F4 4F 0A A9 STP X20, X19, [SP,#0xB0+var_10] .text:000000709EA9550C FD 7B 0B A9 STP X29, X30, [SP,#0xB0+var_s0] .text:000000709EA95510 FD C3 02 91 ADD X29, SP, #0xB0 .text:000000709EA95514 48 D0 3B D5 MRS X8, #3, c13, c0, #2 .text:000000709EA95518 08 15 40 F9 LDR X8, [X8,#0x28] .text:000000709EA9551C F3 03 00 AA MOV X19, X0 .text:000000709EA95520 E8 27 00 F9 STR X8, [SP,#0xB0+var_68] .text:000000709EA95524 68 02 40 F9 LDR X8, [X19] .text:000000709EA95528 69 0A 40 F9 LDR X9, [X19,#0x10] .text:000000709EA9552C 1F 01 09 EB CMP X8, X9 .text:000000709EA95530 6A 1C 01 54 B.GE loc_709EA978BC .text:000000709EA95530 .text:000000709EA95534 7C 16 40 F9 LDR X28, [X19,#0x28] ; 解压后bycode .text:000000709EA95538 77 02 40 F9 LDR X23, [X19] .text:000000709EA9553C 09 02 A0 52 09 21 83 72 MOV W9, #0x101908 .text:000000709EA95544 3A 00 00 D0 ADRP X26, #jpt_709EA958A0@PAGE .text:000000709EA95548 FB 00 00 B0 ADRP X27, #dword_709EAB2008@PAGE .text:000000709EA9554C 5A 43 3B 91 ADD X26, X26, #jpt_709EA958A0@PAGEOFF .text:000000709EA95550 2D 00 09 8B ADD X13, X1, X9 .text:000000709EA95554 FC 37 01 A9 STP X28, X13, [SP,#0xB0+bycode] .text:000000709EA95558 C8 00 00 14 B dsp_loc_786D55A878 ; 取解压后VMbycode解析VMbycode执行对应的Hnadle: 复制代码 隐藏代码 .text:000000709EA95878 dsp_loc_786D55A878 .text:000000709EA95878 15 69 7C B8 LDR W21, [X8,X28] ; 取解压后VMbycode .text:000000709EA9587C A8 72 19 53 UBFX W8, W21, #0x19, #4 .text:000000709EA95880 08 11 00 51 SUB W8, W8, #4 ; switch 12 cases .text:000000709EA95884 75 3E 00 B9 STR W21, [X19,#0x3C] .text:000000709EA95888 B7 01 00 F9 STR X23, [X13] .text:000000709EA9588C 77 0B 00 B9 STR W23, [X27,#dword_709EAB2008@PAGEOFF] .text:000000709EA95890 1F 2D 00 71 CMP W8, #0xB .text:000000709EA95894 68 00 01 54 B.HI dsp_def_786E9038A0 .text:000000709EA95894 .text:000000709EA95898 48 7B A8 B8 LDRSW X8, [X26,X8,LSL#2] .text:000000709EA9589C 08 01 1A 8B ADD X8, X8, X26 .text:000000709EA958A0 00 01 1F D6 BR X8 ; switch jump4.3、常见Handle一览 常见的算术运算 复制代码 隐藏代码 .text:000000709EA93DD8 ADD_sub_709EA93DD8 .text:000000709EA93DD8 ; __unwind { .text:000000709EA93DD8 68 00 02 0B ADD W8, W3, W2 .text:000000709EA93DDC 28 00 00 B9 STR W8, [X1] .text:000000709EA93DE0 C0 03 5F D6 RET 复制代码 隐藏代码 .text:000000709EA93E08 SUB_sub_709EA93E08 .text:000000709EA93E08 ; __unwind { .text:000000709EA93E08 48 00 03 4B SUB W8, W2, W3 .text:000000709EA93E0C 28 00 00 B9 STR W8, [X1] .text:000000709EA93E10 C0 03 5F D6 RET 复制代码 隐藏代码 .text:000000709EA93E20 AND_sub_709EA93E20 .text:000000709EA93E20 ; __unwind { .text:000000709EA93E20 68 00 02 0A AND W8, W3, W2 .text:000000709EA93E24 28 00 00 B9 STR W8, [X1] .text:000000709EA93E28 C0 03 5F D6 RET 复制代码 隐藏代码 .text:000000709EA93E44 EOR_sub_786E901E44 .text:000000709EA93E44 ; __unwind { .text:000000709EA93E44 68 00 02 4A EOR W8, W3, W2 .text:000000709EA93E48 28 00 00 B9 STR W8, [X1] .text:000000709EA93E4C C0 03 5F D6 RET 复制代码 隐藏代码 .text:000000709EA93FAC MUL_sub_709EA93FAC .text:000000709EA93FAC ; __unwind { .text:000000709EA93FAC 68 7C 02 1B MUL W8, W3, W2 .text:000000709EA93FB0 28 00 00 B9 STR W8, [X1] .text:000000709EA93FB4 C0 03 5F D6 RET 复制代码 隐藏代码 .text:000000709EA97B60 getdatabas_sub_786E905B60 .text:000000709EA97B60 .text:000000709EA97B60 var_20= -0x20 .text:000000709EA97B60 var_18= -0x18 .text:000000709EA97B60 var_C= -0xC .text:000000709EA97B60 var_8= -8 .text:000000709EA97B60 var_s0= 0 .text:000000709EA97B60 .text:000000709EA97B60 ; __unwind { .text:000000709EA97B60 FF C3 00 D1 SUB SP, SP, #0x30 .text:000000709EA97B64 FD 7B 02 A9 STP X29, X30, [SP,#0x20+var_s0] .text:000000709EA97B68 FD 83 00 91 ADD X29, SP, #0x20 .text:000000709EA97B6C 49 D0 3B D5 MRS X9, #3, c13, c0, #2 .text:000000709EA97B70 29 15 40 F9 LDR X9, [X9,#0x28] .text:000000709EA97B74 E8 03 00 AA MOV X8, X0 .text:000000709EA97B78 E0 03 1F AA MOV X0, XZR .text:000000709EA97B7C A9 83 1F F8 STUR X9, [X29,#var_8] .text:000000709EA97B80 FF 03 00 F9 STR XZR, [SP,#0x20+var_20] .text:000000709EA97B84 3F 7C 00 71 CMP W1, #0x1F .text:000000709EA97B88 E0 02 00 54 B.EQ loc_709EA97BE4 .text:000000709EA97B88 .text:000000709EA97B8C 3F 74 00 71 CMP W1, #0x1D .text:000000709EA97B90 E1 00 00 54 B.NE loc_709EA97BAC .text:000000709EA97B90 .text:000000709EA97B94 00 21 40 F9 LDR X0, [X8,#0x40] .text:000000709EA97B98 E8 03 00 32 MOV W8, #1 .text:000000709EA97B9C A8 43 1F B8 STUR W8, [X29,#var_C] .text:000000709EA97BA0 E8 03 00 91 MOV X8, SP .text:000000709EA97BA4 E8 07 00 F9 STR X8, [SP,#0x20+var_18] .text:000000709EA97BA8 0A 00 00 14 B loc_709EA97BD0 .text:000000709EA97BA8 .text:000000709EA97BAC loc_709EA97BAC .text:000000709EA97BAC 00 21 40 F9 LDR X0, [X8,#0x40] .text:000000709EA97BB0 3F 78 00 71 CMP W1, #0x1E .text:000000709EA97BB4 61 00 00 54 B.NE loc_709EA97BC0 .text:000000709EA97BB4 .text:000000709EA97BB8 E8 03 1F 32 MOV W8, #2 .text:000000709EA97BBC 02 00 00 14 B loc_709EA97BC4 .text:000000709EA97BBC .text:000000709EA97BC0 .text:000000709EA97BC0 loc_709EA97BC0 .text:000000709EA97BC0 28 1C 03 11 ADD W8, W1, #0xC7 .text:000000709EA97BC0 .text:000000709EA97BC4 .text:000000709EA97BC4 loc_709EA97BC4 .text:000000709EA97BC4 E9 03 00 91 MOV X9, SP .text:000000709EA97BC8 A8 43 1F B8 STUR W8, [X29,#var_C] .text:000000709EA97BCC E9 07 00 F9 STR X9, [SP,#0x20+var_18] .text:000000709EA97BCC .text:000000709EA97BD0 .text:000000709EA97BD0 loc_709EA97BD0 .text:000000709EA97BD0 A1 33 00 D1 SUB X1, X29, #-var_C .text:000000709EA97BD4 E2 23 00 91 ADD X2, SP, #0x20+var_18 .text:000000709EA97BD8 E3 03 00 32 MOV W3, #1 .text:000000709EA97BDC 2A EF FF 97 BL getdatabasse_sub_786E901884 .text:000000709EA97BDC .text:000000709EA97BE0 E0 03 40 F9 LDR X0, [SP,#0x20+var_20] .text:000000709EA97BE0 .text:000000709EA97BE4 .text:000000709EA97BE4 loc_709EA97BE4 .text:000000709EA97BE4 48 D0 3B D5 MRS X8, #3, c13, c0, #2 .text:000000709EA97BE8 08 15 40 F9 LDR X8, [X8,#0x28] .text:000000709EA97BEC A9 83 5F F8 LDUR X9, [X29,#var_8] .text:000000709EA97BF0 1F 01 09 EB CMP X8, X9 .text:000000709EA97BF4 81 00 00 54 B.NE loc_709EA97C04 .text:000000709EA97BF4 .text:000000709EA97BF8 FD 7B 42 A9 LDP X29, X30, [SP,#0x20+var_s0] .text:000000709EA97BFC FF C3 00 91 ADD SP, SP, #0x30 ; '0' .text:000000709EA97C00 C0 03 5F D6 RET以上Handle都是加密时要用到的。 4.4、眺出VM调用其它模块的Handle 复制代码 隐藏代码 .text:000000709EA936C0 call_loc_709EA936C0 .text:000000709EA936C0 FF 03 02 D1 SUB SP, SP, #0x80 .text:000000709EA936C4 20 01 3F D6 BLR X9 ; 调用tongdun.so .text:000000709EA936C4 .text:000000709EA936C8 FF 03 02 91 ADD SP, SP, #0x80 .text:000000709EA936CC E8 E3 40 B9 LDR W8, [SP,#0x2E0+var_200] .text:000000709EA936D0 48 00 00 35 CBNZ W8, loc_709EA936D8 .text:000000709EA936D0 .text:000000709EA936D4 5F 00 00 14 B loc_709EA93850如果不还原算法的话调试时重点关注这个Handle就能大致分析清楚整体的逻辑。如果要做算法还原就得分析每一个Handle。 五、环境检测与设备信息采集5.1、随机数AES加密存放本地 如果是第一次运行APP判断本地是否有随机数ID,如果没有就生成用AES加密存放在三个地方做为钉子文件: 复制代码 隐藏代码 SharedPreferences td-client-id-3 /data/user/0/包名/files/.td-3 /storage/emulated/0/.td-3 存不同的地用不同的AES KEY key bs3ggr0ismnzmdwxkacrq88xs9uj3l06 ykj314o0nd8423k2cimo5fvx0k234sc5 phx7ryl7sjppatga3nfl1caircw6ct79AES加密是反射调用JAVA实现: 复制代码 隐藏代码 .text:000000709EB4EA6C ; R1:原数据,R2:key .text:000000709EB4EA6C AES_sub_786D1CCA6C .text:000000709EB4EA6C var_CC= -0xCC .text:000000709EB4EA6C anonymous_1= -0xC8 .text:000000709EB4EA6C anonymous_2= -0xC0 .text:000000709EB4EA6C anonymous_3= -0xB8 .text:000000709EB4EA6C anonymous_4= -0xB0 .text:000000709EB4EA6C anonymous_5= -0xA8 .text:000000709EB4EA6C anonymous_6= -0xA0 .text:000000709EB4EA6C anonymous_7= -0x98 .text:000000709EB4EA6C anonymous_8= -0x90 .text:000000709EB4EA6C anonymous_9= -0x88 .text:000000709EB4EA6C anonymous_10= -0x80 .text:000000709EB4EA6C anonymous_11= -0x78 .text:000000709EB4EA6C anonymous_12= -0x70 .text:000000709EB4EA6C anonymous_13= -0x68 .text:000000709EB4EA6C anonymous_14= -0x60 .text:000000709EB4EA6C anonymous_15= -0x58 .text:000000709EB4EA6C anonymous_16= -0x50 .text:000000709EB4EA6C anonymous_17= -0x48 .text:000000709EB4EA6C anonymous_18= -0x40 .text:000000709EB4EA6C anonymous_19= -0x38 .text:000000709EB4EA6C anonymous_20= -0x30 .text:000000709EB4EA6C anonymous_21= -0x28 .text:000000709EB4EA6C anonymous_22= -0x20 .text:000000709EB4EA6C anonymous_23= -0x18 .text:000000709EB4EA6C var_10= -0x10 .text:000000709EB4EA6C var_s0= 0 .text:000000709EB4EA6C .text:000000709EB4EA6C ; __unwind { // 1000 .text:000000709EB4EA6C FC 0F 1E F8 STR X28, [SP,#-0x10+var_10]! .text:000000709EB4EA70 FD 7B 01 A9 STP X29, X30, [SP,#0x10+var_s0] .text:000000709EB4EA74 FD 43 00 91 ADD X29, SP, #0x10 .text:000000709EB4EA78 FF 43 08 D1 SUB SP, SP, #0x210 .text:000000709EB4EA7C A8 83 03 D1 SUB X8, X29, #-(var_E5+5) .text:000000709EB4EA80 00 2D 00 F9 STR X0, [X8,#0x58] .text:000000709EB4EA84 01 29 00 F9 STR X1, [X8,#0x50] .text:000000709EB4EA88 02 25 00 F9 STR X2, [X8,#0x48] .text:000000709EB4EA8C 03 21 00 F9 STR X3, [X8,#0x40] .text:000000709EB4EA90 00 29 40 F9 LDR X0, [X8,#0x50] .text:000000709EB4EA94 00 35 00 F9 STR X0, [X8,#0x68] .text:000000709EB4EA98 89 5F 89 52 49 A1+MOV W9, #0xB50A4AFC .text:000000709EB4EA98 B6 72 .text:000000709EB4EAA0 E9 AF 00 B9 STR W9, [SP,#0x220+var_174] .text:000000709EB4EAA4 E8 53 00 F9 STR X8, [SP,#0x220+var_180] .text:000000709EB4EAA8 01 00 00 14 B loc_709EB4EAAC .text:000000709EB4EAA8 .text:000000709EB4EAAC .text:000000709EB4EAAC loc_709EB4EAAC .text:000000709EB4EAAC E8 AF 40 B9 LDR W8, [SP,#0x220+var_174] .text:000000709EB4EAB0 E9 03 08 2A MOV W9, W8 .text:000000709EB4EAB4 4A 7D 9C 52 0A 0F+MOV W10, #0x8878E3EA .text:000000709EB4EAB4 B1 72 .text:000000709EB4EABC 08 01 0A 6B SUBS W8, W8, W10 .text:000000709EB4EAC0 E9 9F 00 B9 STR W9, [SP,#0x220+var_184] .text:000000709EB4EAC4 E8 9B 00 B9 STR W8, [SP,#0x220+var_188] .text:000000709EB4EAC8 00 07 00 54 B.EQ loc_709EB4EBA8 .text:000000709EB4EAC8 .text:000000709EB4EACC 01 00 00 14 B loc_709EB4EAD0 .text:000000709EB4EACC .text:000000709EB4EAD0 .text:000000709EB4EAD0 loc_709EB4EAD0 .text:000000709EB4EAD0 88 5D 86 52 A8 84+MOV W8, #0x9C2532EC .text:000000709EB4EAD0 B3 72 .text:000000709EB4EAD8 E9 9F 40 B9 LDR W9, [SP,#0x220+var_184] .text:000000709EB4EADC 28 01 08 6B SUBS W8, W9, W8 .text:000000709EB4EAE0 E8 97 00 B9 STR W8, [SP,#0x220+var_18C] .text:000000709EB4EAE4 80 3B 00 54 B.EQ loc_709EB4F254 .text:000000709EB4EAE4 .text:000000709EB4EAE8 01 00 00 14 B loc_709EB4EAEC .text:000000709EB4EAE8 .text:000000709EB4EAEC .text:000000709EB4EAEC loc_709EB4EAEC .text:000000709EB4EAEC 88 5F 89 52 48 A1+MOV W8, #0xB50A4AFC .text:000000709EB4EAEC B6 72 .text:000000709EB4EAF4 E9 9F 40 B9 LDR W9, [SP,#0x220+var_184] .text:000000709EB4EAF8 28 01 08 6B SUBS W8, W9, W8 .text:000000709EB4EAFC E8 93 00 B9 STR W8, [SP,#0x220+var_190] .text:000000709EB4EB00 E0 03 00 54 B.EQ loc_709EB4EB7C .text:000000709EB4EB00 .text:000000709EB4EB04 01 00 00 14 B loc_709EB4EB08 .text:000000709EB4EB04 .text:000000709EB4EB08 .text:000000709EB4EB08 loc_709EB4EB08 .text:000000709EB4EB08 A8 61 87 52 48 30+MOV W8, #0xB9823B0D .text:000000709EB4EB08 B7 72 .text:000000709EB4EB10 E9 9F 40 B9 LDR W9, [SP,#0x220+var_184] .text:000000709EB4EB14 28 01 08 6B SUBS W8, W9, W8 .text:000000709EB4EB18 E8 8F 00 B9 STR W8, [SP,#0x220+var_194] .text:000000709EB4EB1C E0 38 00 54 B.EQ loc_709EB4F238 .text:000000709EB4EB1C .text:000000709EB4EB20 01 00 00 14 B loc_709EB4EB24 .text:000000709EB4EB20 .text:000000709EB4EB24 .text:000000709EB4EB24 loc_709EB4EB24 .text:000000709EB4EB24 88 3C 99 52 48 99+MOV W8, #0xCCCAC9E4 .text:000000709EB4EB24 B9 72 .text:000000709EB4EB2C E9 9F 40 B9 LDR W9, [SP,#0x220+var_184] .text:000000709EB4EB30 28 01 08 6B SUBS W8, W9, W8 .text:000000709EB4EB34 E8 8B 00 B9 STR W8, [SP,#0x220+var_198] .text:000000709EB4EB38 E0 04 00 54 B.EQ loc_709EB4EBD4 .text:000000709EB4EB38 .text:000000709EB4EB3C 01 00 00 14 B loc_709EB4EB40 .text:000000709EB4EB3C .text:000000709EB4EB40 .text:000000709EB4EB40 loc_709EB4EB40 .text:000000709EB4EB40 A8 C9 8A 52 E8 1C+MOV W8, #0x48E7564D .text:000000709EB4EB40 A9 72 .text:000000709EB4EB48 E9 9F 40 B9 LDR W9, [SP,#0x220+var_184] .text:000000709EB4EB4C 28 01 08 6B SUBS W8, W9, W8 .text:000000709EB4EB50 E8 87 00 B9 STR W8, [SP,#0x220+var_19C] .text:000000709EB4EB54 E0 40 00 54 B.EQ loc_709EB4F370 .text:000000709EB4EB54 .text:000000709EB4EB58 01 00 00 14 B loc_709EB4EB5C .text:000000709EB4EB58 .text:000000709EB4EB5C .text:000000709EB4EB5C loc_709EB4EB5C .text:000000709EB4EB5C 08 81 97 52 28 4C+MOV W8, #0x5A61BC08 .text:000000709EB4EB5C AB 72 .text:000000709EB4EB64 E9 9F 40 B9 LDR W9, [SP,#0x220+var_184] .text:000000709EB4EB68 28 01 08 6B SUBS W8, W9, W8 .text:000000709EB4EB6C E8 83 00 B9 STR W8, [SP,#0x220+var_1A0] .text:000000709EB4EB70 E0 40 00 54 B.EQ loc_709EB4F38C .text:000000709EB4EB70 .text:000000709EB4EB74 01 00 00 14 B loc_709EB4EB78 .text:000000709EB4EB74 .text:000000709EB4EB78 .text:000000709EB4EB78 loc_709EB4EB78 .text:000000709EB4EB78 0B 02 00 14 B loc_709EB4F3A4 .text:000000709EB4EB78 .text:000000709EB4EB7C .text:000000709EB4EB7C loc_709EB4EB7C .text:000000709EB4EB7C E8 53 40 F9 LDR X8, [SP,#0x220+var_180] .text:000000709EB4EB80 09 35 40 F9 LDR X9, [X8,#0x68] .text:000000709EB4EB84 29 01 00 F1 SUBS X9, X9, #0 .text:000000709EB4EB88 AA C9 8A 52 EA 1C+MOV W10, #0x48E7564D .text:000000709EB4EB88 A9 72 .text:000000709EB4EB90 4B 7D 9C 52 0B 0F+MOV W11, #0x8878E3EA .text:000000709EB4EB90 B1 72 .text:000000709EB4EB98 6A 11 8A 1A CSEL W10, W11, W10, NE .text:000000709EB4EB9C EA AF 00 B9 STR W10, [SP,#0x220+var_174] .text:000000709EB4EBA0 E9 3F 00 F9 STR X9, [SP,#0x220+var_1A8] .text:000000709EB4EBA4 00 02 00 14 B loc_709EB4F3A4 .text:000000709EB4EBA4 .text:000000709EB4EBA8 .text:000000709EB4EBA8 loc_709EB4EBA8 .text:000000709EB4EBA8 E8 53 40 F9 LDR X8, [SP,#0x220+var_180] .text:000000709EB4EBAC 09 25 40 F9 LDR X9, [X8,#0x48] .text:000000709EB4EBB0 29 01 00 F1 SUBS X9, X9, #0 .text:000000709EB4EBB4 AA C9 8A 52 EA 1C+MOV W10, #0x48E7564D .text:000000709EB4EBB4 A9 72 .text:000000709EB4EBBC 8B 3C 99 52 4B 99+MOV W11, #0xCCCAC9E4 .text:000000709EB4EBBC B9 72 .text:000000709EB4EBC4 6A 11 8A 1A CSEL W10, W11, W10, NE .text:000000709EB4EBC8 EA AF 00 B9 STR W10, [SP,#0x220+var_174] .text:000000709EB4EBCC E9 3B 00 F9 STR X9, [SP,#0x220+var_1B0] .text:000000709EB4EBD0 F5 01 00 14 B loc_709EB4F3A4 .text:000000709EB4EBD0 .text:000000709EB4EBD4 .text:000000709EB4EBD4 loc_709EB4EBD4 .text:000000709EB4EBD4 88 03 00 D0 08 81+ADRL X8, td_8162780960521470701 ; "AES" .text:000000709EB4EBD4 39 91 .text:000000709EB4EBDC E9 53 40 F9 LDR X9, [SP,#0x220+var_180] .text:000000709EB4EBE0 28 1D 00 F9 STR X8, [X9,#0x38] .text:000000709EB4EBE4 88 03 00 D0 08 91+ADRL X8, td_18178131887862966684 ; "AES/ECB/PKCS5Padding" .text:000000709EB4EBE4 39 91 .text:000000709EB4EBEC 28 19 00 F9 STR X8, [X9,#0x30] .text:000000709EB4EBF0 20 2D 40 F9 LDR X0, [X9,#0x58] .text:000000709EB4EBF4 21 1D 40 F9 LDR X1, [X9,#0x38] .text:000000709EB4EBF8 BB 68 00 94 BL NewStringUTF_sub_786D1E6EE4 .text:000000709EB4EBF8 .text:000000709EB4EBFC E8 53 40 F9 LDR X8, [SP,#0x220+var_180] .text:000000709EB4EC00 00 15 00 F9 STR X0, [X8,#0x28] .text:000000709EB4EC04 00 2D 40 F9 LDR X0, [X8,#0x58] .text:000000709EB4EC08 01 19 40 F9 LDR X1, [X8,#0x30] .text:000000709EB4EC0C B6 68 00 94 BL NewStringUTF_sub_786D1E6EE4 .text:000000709EB4EC0C .text:000000709EB4EC10 E8 53 40 F9 LDR X8, [SP,#0x220+var_180] .text:000000709EB4EC14 00 11 00 F9 STR X0, [X8,#0x20] .text:000000709EB4EC18 00 2D 40 F9 LDR X0, [X8,#0x58] .text:000000709EB4EC1C EA 03 1B 32 MOV W10, #0x20 ; ' ' .text:000000709EB4EC20 E1 03 0A 2A MOV W1, W10 .text:000000709EB4EC24 EA 6F 00 B9 STR W10, [SP,#0x220+var_1B4] .text:000000709EB4EC28 98 69 00 94 BL NewByteArray_sub_786D1E7288 .text:000000709EB4EC28 .text:000000709EB4EC2C E8 53 40 F9 LDR X8, [SP,#0x220+var_180] .text:000000709EB4EC30 00 0D 00 F9 STR X0, [X8,#0x18] .text:000000709EB4EC34 00 2D 40 F9 LDR X0, [X8,#0x58] .text:000000709EB4EC38 01 0D 40 F9 LDR X1, [X8,#0x18] .text:000000709EB4EC3C 04 25 40 F9 LDR X4, [X8,#0x48] .text:000000709EB4EC40 EA 03 1F 2A MOV W10, WZR .text:000000709EB4EC44 E2 03 0A 2A MOV W2, W10 .text:000000709EB4EC48 E3 6F 40 B9 LDR W3, [SP,#0x220+var_1B4] .text:000000709EB4EC4C EA 6B 00 B9 STR W10, [SP,#0x220+var_1B8] .text:000000709EB4EC50 BC 69 00 94 BL SetByteArrayRegion_sub_786D1E7340 .text:000000709EB4EC50 .text:000000709EB4EC54 E8 53 40 F9 LDR X8, [SP,#0x220+var_180] .text:000000709EB4EC58 00 29 40 F9 LDR X0, [X8,#0x50] ; s .text:000000709EB4EC5C DD 45 FE 97 BL .strlen .text:000000709EB4EC5C .text:000000709EB4EC60 EA 03 00 2A MOV W10, W0 .text:000000709EB4EC64 AA 43 13 B8 STUR W10, [X29,#var_CC] .text:000000709EB4EC68 E8 53 40 F9 LDR X8, [SP,#0x220+var_180] .text:000000709EB4EC6C 00 2D 40 F9 LDR X0, [X8,#0x58] .text:000000709EB4EC70 A1 43 53 B8 LDUR W1, [X29,#var_CC] .text:000000709EB4EC74 85 69 00 94 BL NewByteArray_sub_786D1E7288 .text:000000709EB4EC74 .text:000000709EB4EC78 E8 53 40 F9 LDR X8, [SP,#0x220+var_180] .text:000000709EB4EC7C 00 05 00 F9 STR X0, [X8,#8] .text:000000709EB4EC80 00 2D 40 F9 LDR X0, [X8,#0x58] .text:000000709EB4EC84 01 05 40 F9 LDR X1, [X8,#8] .text:000000709EB4EC88 A3 43 53 B8 LDUR W3, [X29,#var_CC] .text:000000709EB4EC8C 04 29 40 F9 LDR X4, [X8,#0x50] .text:000000709EB4EC90 E2 6B 40 B9 LDR W2, [SP,#0x220+var_1B8] .text:000000709EB4EC94 AB 69 00 94 BL SetByteArrayRegion_sub_786D1E7340 .text:000000709EB4EC94 .text:000000709EB4EC98 E8 53 40 F9 LDR X8, [SP,#0x220+var_180] .text:000000709EB4EC9C 09 2D 40 F9 LDR X9, [X8,#0x58] .text:000000709EB4ECA0 CA 14 80 52 MOV W10, #0xA6 .text:000000709EB4ECA4 AA 03 10 38 STURB W10, [X29,#var_100] .text:000000709EB4ECA8 CA 02 80 52 MOV W10, #0x16 .text:000000709EB4ECAC AA 13 10 38 STURB W10, [X29,#var_FF] .text:000000709EB4ECB0 E2 0C 80 52 MOV W2, #0x67 ; 'g' .text:000000709EB4ECB4 A2 23 10 38 STURB W2, [X29,#var_FE] .text:000000709EB4ECB8 AA 33 10 38 STURB W10, [X29,#var_FD] .text:000000709EB4ECBC EA 10 80 52 MOV W10, #0x87 .text:000000709EB4ECC0 AA 43 10 38 STURB W10, [X29,#var_FC] .text:000000709EB4ECC4 4A 1E 80 52 MOV W10, #0xF2 .text:000000709EB4ECC8 AA 53 10 38 STURB W10, [X29,#var_FB] .text:000000709EB4ECCC C2 06 80 52 MOV W2, #0x36 ; '6' .text:000000709EB4ECD0 A2 63 10 38 STURB W2, [X29,#var_FA] .text:000000709EB4ECD4 E3 04 80 52 MOV W3, #0x27 ; ''' .text:000000709EB4ECD8 A3 73 10 38 STURB W3, [X29,#var_F9] .text:000000709EB4ECDC EB 12 80 52 MOV W11, #0x97 .text:000000709EB4ECE0 AB 83 10 38 STURB W11, [X29,#var_F8] .text:000000709EB4ECE4 EC 0B 00 32 MOV W12, #7 .text:000000709EB4ECE8 AC 93 10 38 STURB W12, [X29,#var_F7] .text:000000709EB4ECEC ED 08 80 52 MOV W13, #0x47 ; 'G' .text:000000709EB4ECF0 AD A3 10 38 STURB W13, [X29,#var_F6] .text:000000709EB4ECF4 CE 1E 80 52 MOV W14, #0xF6 .text:000000709EB4ECF8 AE B3 10 38 STURB W14, [X29,#var_F5] .text:000000709EB4ECFC AA C3 10 38 STURB W10, [X29,#var_F4] .text:000000709EB4ED00 EE 06 80 52 MOV W14, #0x37 ; '7' .text:000000709EB4ED04 AE D3 10 38 STURB W14, [X29,#var_F3] .text:000000709EB4ED08 AC E3 10 38 STURB W12, [X29,#var_F2] .text:000000709EB4ED0C CE 0A 80 52 MOV W14, #0x56 ; 'V' .text:000000709EB4ED10 AE F3 10 38 STURB W14, [X29,#var_F1] .text:000000709EB4ED14 A2 03 11 38 STURB W2, [X29,#var_F0] .text:000000709EB4ED18 AA 13 11 38 STURB W10, [X29,#var_EF] .text:000000709EB4ED1C AA 06 80 52 MOV W10, #0x35 ; '5' .text:000000709EB4ED20 AA 23 11 38 STURB W10, [X29,#var_EE] .text:000000709EB4ED24 AE 33 11 38 STURB W14, [X29,#var_ED] .text:000000709EB4ED28 A2 43 11 38 STURB W2, [X29,#var_EC] .text:000000709EB4ED2C A3 53 11 38 STURB W3, [X29,#var_EB] .text:000000709EB4ED30 AE 63 11 38 STURB W14, [X29,#var_EA] .text:000000709EB4ED34 AD 73 11 38 STURB W13, [X29,#var_E9] .text:000000709EB4ED38 8D 16 80 52 MOV W13, #0xB4 .text:000000709EB4ED3C AD 83 11 38 STURB W13, [X29,#var_E8] .text:000000709EB4ED40 AE 93 11 38 STURB W14, [X29,#var_E7] .text:000000709EB4ED44 AB A3 11 38 STURB W11, [X29,#var_E6] .text:000000709EB4ED48 AA B3 11 38 STURB W10, [X29,#var_E5] .text:000000709EB4ED4C AC C3 11 38 STURB W12, [X29,#var_E5+1] .text:000000709EB4ED50 AE D3 11 38 STURB W14, [X29,#var_E5+2] .text:000000709EB4ED54 A2 E3 11 38 STURB W2, [X29,#var_E5+3] .text:000000709EB4ED58 EA 6B 40 B9 LDR W10, [SP,#0x220+var_1B8] .text:000000709EB4ED5C AA F3 11 38 STURB W10, [X29,#var_E5+4] .text:000000709EB4ED60 A0 03 04 D1 SUB X0, X29, #-var_100 .text:000000709EB4ED64 00 3D 00 F9 STR X0, [X8,#0x78] .text:000000709EB4ED68 00 3D 40 F9 LDR X0, [X8,#0x78] .text:000000709EB4ED6C 00 39 00 F9 STR X0, [X8,#0x70] .text:000000709EB4ED70 E9 33 00 F9 STR X9, [SP,#0x220+var_1C0] .text:000000709EB4ED74 01 00 00 14 B loc_709EB4ED78 .text:000000709EB4ED74 .text:000000709EB4ED78 .text:000000709EB4ED78 loc_709EB4ED78 .text:000000709EB4ED78 E8 53 40 F9 LDR X8, [SP,#0x220+var_180] .text:000000709EB4ED7C 09 3D 40 F9 LDR X9, [X8,#0x78] .text:000000709EB4ED80 2A 01 40 39 LDRB W10, [X9] .text:000000709EB4ED84 8A 01 00 34 CBZ W10, loc_709EB4EDB4 .text:000000709EB4ED84 .text:000000709EB4ED88 01 00 00 14 B loc_709EB4ED8C .text:000000709EB4ED8C .text:000000709EB4ED8C loc_709EB4ED8C .text:000000709EB4ED8C E8 53 40 F9 LDR X8, [SP,#0x220+var_180] .text:000000709EB4ED90 09 3D 40 F9 LDR X9, [X8,#0x78] .text:000000709EB4ED94 2A 01 40 39 LDRB W10, [X9] .text:000000709EB4ED98 4B 7D 04 53 LSR W11, W10, #4 .text:000000709EB4ED9C 4B 1D 1C 33 BFI W11, W10, #4, #8 .text:000000709EB4EDA0 2B 01 00 39 STRB W11, [X9] .text:000000709EB4EDA4 09 3D 40 F9 LDR X9, [X8,#0x78] .text:000000709EB4EDA8 29 05 00 91 ADD X9, X9, #1 .text:000000709EB4EDAC 09 3D 00 F9 STR X9, [X8,#0x78] .text:000000709EB4EDB0 F2 FF FF 17 B loc_709EB4ED78 .text:000000709EB4EDB0 .text:000000709EB4EDB4 .text:000000709EB4EDB4 loc_709EB4EDB4 .text:000000709EB4EDB4 E8 53 40 F9 LDR X8, [SP,#0x220+var_180] .text:000000709EB4EDB8 01 39 40 F9 LDR X1, [X8,#0x70] .text:000000709EB4EDBC E0 33 40 F9 LDR X0, [SP,#0x220+var_1C0] .text:000000709EB4EDC0 8E 69 00 94 BL FindClass_sub_786D1E73F8 .text:000000709EB4EDC0 .text:000000709EB4EDC4 E8 53 40 F9 LDR X8, [SP,#0x220+var_180] .text:000000709EB4EDC8 00 01 00 F9 STR X0, [X8] .text:000000709EB4EDCC 00 2D 40 F9 LDR X0, [X8,#0x58] .text:000000709EB4EDD0 01 01 40 F9 LDR X1, [X8] .text:000000709EB4EDD4 04 0D 40 F9 LDR X4, [X8,#0x18] .text:000000709EB4EDD8 05 15 40 F9 LDR X5, [X8,#0x28] .text:000000709EB4EDDC 42 01 00 D0 42 98+ADRL X2, td_9741829121851609613 ; "" .text:000000709EB4EDDC 32 91 .text:000000709EB4EDE4 43 01 00 D0 63 B4+ADRL X3, td_1727475097158774760 ; "([BLjava/lang/String;)V" .text:000000709EB4EDE4 32 91 .text:000000709EB4EDEC B3 01 00 94 BL CallVoidMethod_sub_786D1CD4B8 .text:000000709EB4EDEC .text:000000709EB4EDF0 E0 8F 00 F9 STR X0, [SP,#0x220+var_108] .text:000000709EB4EDF4 E8 53 40 F9 LDR X8, [SP,#0x220+var_180] .text:000000709EB4EDF8 00 2D 40 F9 LDR X0, [X8,#0x58] .text:000000709EB4EDFC C9 14 80 52 MOV W9, #0xA6 .text:000000709EB4EE00 E9 F3 03 39 STRB W9, [SP,#0xFC] .text:000000709EB4EE04 C9 02 80 52 MOV W9, #0x16 .text:000000709EB4EE08 E9 F7 03 39 STRB W9, [SP,#0xFD] .text:000000709EB4EE0C EA 0C 80 52 MOV W10, #0x67 ; 'g' .text:000000709EB4EE10 EA FB 03 39 STRB W10, [SP,#0xFE] .text:000000709EB4EE14 E9 FF 03 39 STRB W9, [SP,#0x220+var_121] .text:000000709EB4EE18 E9 10 80 52 MOV W9, #0x87 .text:000000709EB4EE1C E9 03 04 39 STRB W9, [SP,#0x220+var_120] .text:000000709EB4EE20 49 1E 80 52 MOV W9, #0xF2 .text:000000709EB4EE24 E9 07 04 39 STRB W9, [SP,#0x220+var_11F] .text:000000709EB4EE28 CA 06 80 52 MOV W10, #0x36 ; '6' .text:000000709EB4EE2C EA 0B 04 39 STRB W10, [SP,#0x220+var_11E] .text:000000709EB4EE30 EA 04 80 52 MOV W10, #0x27 ; ''' .text:000000709EB4EE34 EA 0F 04 39 STRB W10, [SP,#0x220+var_11D] .text:000000709EB4EE38 EB 12 80 52 MOV W11, #0x97 .text:000000709EB4EE3C EB 13 04 39 STRB W11, [SP,#0x220+var_11C] .text:000000709EB4EE40 EB 0B 00 32 MOV W11, #7 .text:000000709EB4EE44 EB 17 04 39 STRB W11, [SP,#0x220+var_11B] .text:000000709EB4EE48 EC 08 80 52 MOV W12, #0x47 ; 'G' .text:000000709EB4EE4C EC 1B 04 39 STRB W12, [SP,#0x220+var_11A] .text:000000709EB4EE50 CC 1E 80 52 MOV W12, #0xF6 .text:000000709EB4EE54 EC 1F 04 39 STRB W12, [SP,#0x220+var_119] .text:000000709EB4EE58 E9 23 04 39 STRB W9, [SP,#0x220+var_118] .text:000000709EB4EE5C 89 06 80 52 MOV W9, #0x34 ; '4' .text:000000709EB4EE60 E9 27 04 39 STRB W9, [SP,#0x220+var_117] .text:000000709EB4EE64 C9 12 80 52 MOV W9, #0x96 .text:000000709EB4EE68 E9 2B 04 39 STRB W9, [SP,#0x220+var_116] .text:000000709EB4EE6C EB 2F 04 39 STRB W11, [SP,#0x220+var_115] .text:000000709EB4EE70 C9 10 80 52 MOV W9, #0x86 .text:000000709EB4EE74 E9 33 04 39 STRB W9, [SP,#0x220+var_114] .text:000000709EB4EE78 C9 0A 80 52 MOV W9, #0x56 ; 'V' .text:000000709EB4EE7C E9 37 04 39 STRB W9, [SP,#0x220+var_113] .text:000000709EB4EE80 EA 3B 04 39 STRB W10, [SP,#0x220+var_113+1] .text:000000709EB4EE84 E9 03 1F 2A MOV W9, WZR .text:000000709EB4EE88 E9 3F 04 39 STRB W9, [SP,#0x220+var_113+2] .text:000000709EB4EE8C E1 F3 03 91 ADD X1, SP, #0xFC .text:000000709EB4EE90 01 65 00 F9 STR X1, [X8,#0xC8] .text:000000709EB4EE94 01 65 40 F9 LDR X1, [X8,#0xC8] .text:000000709EB4EE98 01 61 00 F9 STR X1, [X8,#0xC0] .text:000000709EB4EE9C E0 2F 00 F9 STR X0, [SP,#0x220+var_1C8] .text:000000709EB4EEA0 01 00 00 14 B loc_709EB4EEA4 .text:000000709EB4EEA0 .text:000000709EB4EEA4 .text:000000709EB4EEA4 loc_709EB4EEA4 .text:000000709EB4EEA4 E8 53 40 F9 LDR X8, [SP,#0x220+var_180] .text:000000709EB4EEA8 09 65 40 F9 LDR X9, [X8,#0xC8] .text:000000709EB4EEAC 2A 01 40 39 LDRB W10, [X9] .text:000000709EB4EEB0 8A 01 00 34 CBZ W10, loc_709EB4EEE0 .text:000000709EB4EEB0 .text:000000709EB4EEB4 01 00 00 14 B loc_709EB4EEB8 .text:000000709EB4EEB4 .text:000000709EB4EEB8 .text:000000709EB4EEB8 loc_709EB4EEB8 .text:000000709EB4EEB8 E8 53 40 F9 LDR X8, [SP,#0x220+var_180] .text:000000709EB4EEBC 09 65 40 F9 LDR X9, [X8,#0xC8] .text:000000709EB4EEC0 2A 01 40 39 LDRB W10, [X9] .text:000000709EB4EEC4 4B 7D 04 53 LSR W11, W10, #4 .text:000000709EB4EEC8 4B 1D 1C 33 BFI W11, W10, #4, #8 .text:000000709EB4EECC 2B 01 00 39 STRB W11, [X9] .text:000000709EB4EED0 09 65 40 F9 LDR X9, [X8,#0xC8] .text:000000709EB4EED4 29 05 00 91 ADD X9, X9, #1 .text:000000709EB4EED8 09 65 00 F9 STR X9, [X8,#0xC8] .text:000000709EB4EEDC F2 FF FF 17 B loc_709EB4EEA4 .text:000000709EB4EEE0 .text:000000709EB4EEE0 loc_709EB4EEE0 .text:000000709EB4EEE0 E8 53 40 F9 LDR X8, [SP,#0x220+var_180] .text:000000709EB4EEE4 01 61 40 F9 LDR X1, [X8,#0xC0] .text:000000709EB4EEE8 04 11 40 F9 LDR X4, [X8,#0x20] .text:000000709EB4EEEC 02 03 00 B0 42 D0+ADRL X2, td_4822081916216048550 ; "getInstance" .text:000000709EB4EEEC 11 91 .text:000000709EB4EEF4 03 03 00 B0 63 BC+ADRL X3, td_12347290237301947307 ; "(Ljava/lang/String;)Ljavax/crypto/Ciphe"... .text:000000709EB4EEF4 12 91 .text:000000709EB4EEFC E0 2F 40 F9 LDR X0, [SP,#0x220+var_1C8] .text:000000709EB4EF00 80 01 00 94 BL CallVoidMethod_sub_786D1CD500 .text:000000709EB4EF00 .text:000000709EB4EF04 E0 8B 00 F9 STR X0, [SP,#0x220+var_113+3] .text:000000709EB4EF08 E8 53 40 F9 LDR X8, [SP,#0x220+var_180] .text:000000709EB4EF0C 00 2D 40 F9 LDR X0, [X8,#0x58] .text:000000709EB4EF10 E1 8B 40 F9 LDR X1, [SP,#0x220+var_113+3] .text:000000709EB4EF14 C9 12 80 52 MOV W9, #0x96 .text:000000709EB4EF18 E9 D3 03 39 STRB W9, [SP,#0x220+var_12E+2] .text:000000709EB4EF1C CA 1C 80 52 MOV W10, #0xE6 .text:000000709EB4EF20 EA D7 03 39 STRB W10, [SP,#0x220+var_12E+3] .text:000000709EB4EF24 E9 DB 03 39 STRB W9, [SP,#0x220+var_12E+4] .text:000000709EB4EF28 E9 08 80 52 MOV W9, #0x47 ; 'G' .text:000000709EB4EF2C E9 DF 03 39 STRB W9, [SP,#0x220+var_12E+5] .text:000000709EB4EF30 E9 03 1F 2A MOV W9, WZR .text:000000709EB4EF34 E9 E3 03 39 STRB W9, [SP,#0x220+var_12E+6] .text:000000709EB4EF38 E2 D3 03 91 ADD X2, SP, #0x220+var_12E+2 .text:000000709EB4EF3C 02 5D 00 F9 STR X2, [X8,#0xB8] .text:000000709EB4EF40 02 5D 40 F9 LDR X2, [X8,#0xB8] .text:000000709EB4EF44 02 59 00 F9 STR X2, [X8,#0xB0] .text:000000709EB4EF48 E0 2B 00 F9 STR X0, [SP,#0x220+var_1D0] .text:000000709EB4EF4C E1 27 00 F9 STR X1, [SP,#0x220+var_1D8] .text:000000709EB4EF50 01 00 00 14 B loc_709EB4EF54 .text:000000709EB4EF50 .text:000000709EB4EF54 .text:000000709EB4EF54 loc_709EB4EF54 .text:000000709EB4EF54 E8 53 40 F9 LDR X8, [SP,#0x220+var_180] .text:000000709EB4EF58 09 5D 40 F9 LDR X9, [X8,#0xB8] .text:000000709EB4EF5C 2A 01 40 39 LDRB W10, [X9] .text:000000709EB4EF60 8A 01 00 34 CBZ W10, loc_709EB4EF90 .text:000000709EB4EF60 .text:000000709EB4EF64 01 00 00 14 B loc_709EB4EF68 .text:000000709EB4EF64 .text:000000709EB4EF68 .text:000000709EB4EF68 loc_709EB4EF68 .text:000000709EB4EF68 E8 53 40 F9 LDR X8, [SP,#0x220+var_180] .text:000000709EB4EF6C 09 5D 40 F9 LDR X9, [X8,#0xB8] .text:000000709EB4EF70 2A 01 40 39 LDRB W10, [X9] .text:000000709EB4EF74 4B 7D 04 53 LSR W11, W10, #4 .text:000000709EB4EF78 4B 1D 1C 33 BFI W11, W10, #4, #8 .text:000000709EB4EF7C 2B 01 00 39 STRB W11, [X9] .text:000000709EB4EF80 09 5D 40 F9 LDR X9, [X8,#0xB8] .text:000000709EB4EF84 29 05 00 91 ADD X9, X9, #1 .text:000000709EB4EF88 09 5D 00 F9 STR X9, [X8,#0xB8] .text:000000709EB4EF8C F2 FF FF 17 B loc_709EB4EF54 .text:000000709EB4EF8C .text:000000709EB4EF90 .text:000000709EB4EF90 loc_709EB4EF90 .text:000000709EB4EF90 E8 53 40 F9 LDR X8, [SP,#0x220+var_180] .text:000000709EB4EF94 09 59 40 F9 LDR X9, [X8,#0xB0] .text:000000709EB4EF98 4A 10 80 52 MOV W10, #0x82 .text:000000709EB4EF9C EA 73 03 39 STRB W10, [SP,#0x220+var_144] .text:000000709EB4EFA0 8A 12 80 52 MOV W10, #0x94 .text:000000709EB4EFA4 EA 77 03 39 STRB W10, [SP,#0x220+var_143] .text:000000709EB4EFA8 8A 18 80 52 MOV W10, #0xC4 .text:000000709EB4EFAC EA 7B 03 39 STRB W10, [SP,#0x220+var_142] .text:000000709EB4EFB0 CA 14 80 52 MOV W10, #0xA6 .text:000000709EB4EFB4 EA 7F 03 39 STRB W10, [SP,#0x220+var_141] .text:000000709EB4EFB8 CA 02 80 52 MOV W10, #0x16 .text:000000709EB4EFBC EA 83 03 39 STRB W10, [SP,#0x220+var_140] .text:000000709EB4EFC0 EB 0C 80 52 MOV W11, #0x67 ; 'g' .text:000000709EB4EFC4 EB 87 03 39 STRB W11, [SP,#0x220+var_13F] .text:000000709EB4EFC8 EA 8B 03 39 STRB W10, [SP,#0x220+var_13E] .text:000000709EB4EFCC 4A 1E 80 52 MOV W10, #0xF2 .text:000000709EB4EFD0 EA 8F 03 39 STRB W10, [SP,#0x220+var_13D] .text:000000709EB4EFD4 EB 06 80 52 MOV W11, #0x37 ; '7' .text:000000709EB4EFD8 EB 93 03 39 STRB W11, [SP,#0x220+var_13C] .text:000000709EB4EFDC CB 0A 80 52 MOV W11, #0x56 ; 'V' .text:000000709EB4EFE0 EB 97 03 39 STRB W11, [SP,#0x220+var_13B] .text:000000709EB4EFE4 CC 06 80 52 MOV W12, #0x36 ; '6' .text:000000709EB4EFE8 EC 9B 03 39 STRB W12, [SP,#0x220+var_13A] .text:000000709EB4EFEC EC 0A 80 52 MOV W12, #0x57 ; 'W' .text:000000709EB4EFF0 EC 9F 03 39 STRB W12, [SP,#0x220+var_139] .text:000000709EB4EFF4 EC 04 80 52 MOV W12, #0x27 ; ''' .text:000000709EB4EFF8 EC A3 03 39 STRB W12, [SP,#0x220+var_138] .text:000000709EB4EFFC CC 12 80 52 MOV W12, #0x96 .text:000000709EB4F000 EC A7 03 39 STRB W12, [SP,#0x220+var_137] .text:000000709EB4F004 EC 08 80 52 MOV W12, #0x47 ; 'G' .text:000000709EB4F008 EC AB 03 39 STRB W12, [SP,#0x220+var_136] .text:000000709EB4F00C EC 12 80 52 MOV W12, #0x97 .text:000000709EB4F010 EC AF 03 39 STRB W12, [SP,#0x220+var_135] .text:000000709EB4F014 EA B3 03 39 STRB W10, [SP,#0x220+var_134] .text:000000709EB4F018 8A 16 80 52 MOV W10, #0xB4 .text:000000709EB4F01C EA B7 03 39 STRB W10, [SP,#0x220+var_133] .text:000000709EB4F020 EB BB 03 39 STRB W11, [SP,#0x220+var_132] .text:000000709EB4F024 EC BF 03 39 STRB W12, [SP,#0x220+var_131] .text:000000709EB4F028 6A 16 80 52 MOV W10, #0xB3 .text:000000709EB4F02C EA C3 03 39 STRB W10, [SP,#0x220+var_130] .text:000000709EB4F030 4A 12 80 52 MOV W10, #0x92 .text:000000709EB4F034 EA C7 03 39 STRB W10, [SP,#0x220+var_12F] .text:000000709EB4F038 AA 0C 80 52 MOV W10, #0x65 ; 'e' .text:000000709EB4F03C EA CB 03 39 STRB W10, [SP,#0x220+var_12E] .text:000000709EB4F040 EA 03 1F 2A MOV W10, WZR .text:000000709EB4F044 EA CF 03 39 STRB W10, [SP,#0x220+var_12E+1] .text:000000709EB4F048 ED 73 03 91 ADD X13, SP, #0x220+var_144 .text:000000709EB4F04C 0D 55 00 F9 STR X13, [X8,#0xA8] .text:000000709EB4F050 0D 55 40 F9 LDR X13, [X8,#0xA8] .text:000000709EB4F054 0D 51 00 F9 STR X13, [X8,#0xA0] .text:000000709EB4F058 E9 23 00 F9 STR X9, [SP,#0x220+var_1E0] .text:000000709EB4F05C 01 00 00 14 B loc_709EB4F060 .text:000000709EB4F060 .text:000000709EB4F060 loc_709EB4F060 .text:000000709EB4F060 E8 53 40 F9 LDR X8, [SP,#0x220+var_180] .text:000000709EB4F064 09 55 40 F9 LDR X9, [X8,#0xA8] .text:000000709EB4F068 2A 01 40 39 LDRB W10, [X9] .text:000000709EB4F06C 8A 01 00 34 CBZ W10, loc_709EB4F09C .text:000000709EB4F06C .text:000000709EB4F070 01 00 00 14 B loc_709EB4F074 .text:000000709EB4F074 .text:000000709EB4F074 loc_709EB4F074 .text:000000709EB4F074 E8 53 40 F9 LDR X8, [SP,#0x220+var_180] .text:000000709EB4F078 09 55 40 F9 LDR X9, [X8,#0xA8] .text:000000709EB4F07C 2A 01 40 39 LDRB W10, [X9] .text:000000709EB4F080 4B 7D 04 53 LSR W11, W10, #4 .text:000000709EB4F084 4B 1D 1C 33 BFI W11, W10, #4, #8 .text:000000709EB4F088 2B 01 00 39 STRB W11, [X9] .text:000000709EB4F08C 09 55 40 F9 LDR X9, [X8,#0xA8] .text:000000709EB4F090 29 05 00 91 ADD X9, X9, #1 .text:000000709EB4F094 09 55 00 F9 STR X9, [X8,#0xA8] .text:000000709EB4F098 F2 FF FF 17 B loc_709EB4F060 .text:000000709EB4F09C .text:000000709EB4F09C loc_709EB4F09C .text:000000709EB4F09C E8 53 40 F9 LDR X8, [SP,#0x220+var_180] .text:000000709EB4F0A0 03 51 40 F9 LDR X3, [X8,#0xA0] .text:000000709EB4F0A4 E5 8F 40 F9 LDR X5, [SP,#0x220+var_108] .text:000000709EB4F0A8 E4 03 00 32 MOV W4, #1 .text:000000709EB4F0AC E0 2B 40 F9 LDR X0, [SP,#0x220+var_1D0] .text:000000709EB4F0B0 E1 27 40 F9 LDR X1, [SP,#0x220+var_1D8] .text:000000709EB4F0B4 E2 23 40 F9 LDR X2, [SP,#0x220+var_1E0] .text:000000709EB4F0B8 22 01 00 94 BL CallVoidMethod_sub_786D1CD540 .text:000000709EB4F0B8 .text:000000709EB4F0BC E8 53 40 F9 LDR X8, [SP,#0x220+var_180] .text:000000709EB4F0C0 01 2D 40 F9 LDR X1, [X8,#0x58] .text:000000709EB4F0C4 E2 8B 40 F9 LDR X2, [SP,#0x220+var_113+3] .text:000000709EB4F0C8 C4 08 80 52 MOV W4, #0x46 ; 'F' .text:000000709EB4F0CC E4 23 03 39 STRB W4, [SP,#0x220+var_15B+3] .text:000000709EB4F0D0 C4 1E 80 52 MOV W4, #0xF6 .text:000000709EB4F0D4 E4 27 03 39 STRB W4, [SP,#0x220+var_15B+4] .text:000000709EB4F0D8 84 0C 80 52 MOV W4, #0x64 ; 'd' .text:000000709EB4F0DC E4 2B 03 39 STRB W4, [SP,#0x220+var_15B+5] .text:000000709EB4F0E0 C4 12 80 52 MOV W4, #0x96 .text:000000709EB4F0E4 E4 2F 03 39 STRB W4, [SP,#0x220+var_15B+6] .text:000000709EB4F0E8 C4 1C 80 52 MOV W4, #0xE6 .text:000000709EB4F0EC E4 33 03 39 STRB W4, [SP,#0x220+var_15B+7] .text:000000709EB4F0F0 C4 02 80 52 MOV W4, #0x16 .text:000000709EB4F0F4 E4 37 03 39 STRB W4, [SP,#0x220+var_153] .text:000000709EB4F0F8 C4 18 80 52 MOV W4, #0xC6 .text:000000709EB4F0FC E4 3B 03 39 STRB W4, [SP,#0x220+var_152] .text:000000709EB4F100 E4 03 1F 2A MOV W4, WZR .text:000000709EB4F104 E4 3F 03 39 STRB W4, [SP,#0x220+var_151] .text:000000709EB4F108 E3 23 03 91 ADD X3, SP, #0x220+var_15B+3 .text:000000709EB4F10C 03 4D 00 F9 STR X3, [X8,#0x98] .text:000000709EB4F110 03 4D 40 F9 LDR X3, [X8,#0x98] .text:000000709EB4F114 03 49 00 F9 STR X3, [X8,#0x90] .text:000000709EB4F118 E0 3F 00 B9 STR W0, [SP,#0x220+var_1E4] .text:000000709EB4F11C E1 1B 00 F9 STR X1, [SP,#0x220+var_1F0] .text:000000709EB4F120 E2 17 00 F9 STR X2, [SP,#0x220+var_1F8] .text:000000709EB4F124 01 00 00 14 B loc_709EB4F128 .text:000000709EB4F124 .text:000000709EB4F128 .text:000000709EB4F128 loc_709EB4F128 .text:000000709EB4F128 ; AES_sub_786D1CCA6C+6F4↓j .text:000000709EB4F128 E8 53 40 F9 LDR X8, [SP,#0x220+var_180] .text:000000709EB4F12C 09 4D 40 F9 LDR X9, [X8,#0x98] .text:000000709EB4F130 2A 01 40 39 LDRB W10, [X9] .text:000000709EB4F134 8A 01 00 34 CBZ W10, loc_709EB4F164 .text:000000709EB4F134 .text:000000709EB4F138 01 00 00 14 B loc_709EB4F13C .text:000000709EB4F138 .text:000000709EB4F13C .text:000000709EB4F13C loc_709EB4F13C .text:000000709EB4F13C E8 53 40 F9 LDR X8, [SP,#0x220+var_180] .text:000000709EB4F140 09 4D 40 F9 LDR X9, [X8,#0x98] .text:000000709EB4F144 2A 01 40 39 LDRB W10, [X9] .text:000000709EB4F148 4B 7D 04 53 LSR W11, W10, #4 .text:000000709EB4F14C 4B 1D 1C 33 BFI W11, W10, #4, #8 .text:000000709EB4F150 2B 01 00 39 STRB W11, [X9] .text:000000709EB4F154 09 4D 40 F9 LDR X9, [X8,#0x98] .text:000000709EB4F158 29 05 00 91 ADD X9, X9, #1 .text:000000709EB4F15C 09 4D 00 F9 STR X9, [X8,#0x98] .text:000000709EB4F160 F2 FF FF 17 B loc_709EB4F128 .text:000000709EB4F160 .text:000000709EB4F164 .text:000000709EB4F164 loc_709EB4F164 .text:000000709EB4F164 E8 53 40 F9 LDR X8, [SP,#0x220+var_180] .text:000000709EB4F168 09 49 40 F9 LDR X9, [X8,#0x90] .text:000000709EB4F16C 4A 10 80 52 MOV W10, #0x82 .text:000000709EB4F170 EA 03 03 39 STRB W10, [SP,#0x220+var_160] .text:000000709EB4F174 AA 16 80 52 MOV W10, #0xB5 .text:000000709EB4F178 EA 07 03 39 STRB W10, [SP,#0x220+var_15F] .text:000000709EB4F17C 8B 04 80 52 MOV W11, #0x24 ; '$' .text:000000709EB4F180 EB 0B 03 39 STRB W11, [SP,#0x220+var_15E] .text:000000709EB4F184 4C 12 80 52 MOV W12, #0x92 .text:000000709EB4F188 EC 0F 03 39 STRB W12, [SP,#0x220+var_15D] .text:000000709EB4F18C EA 13 03 39 STRB W10, [SP,#0x220+var_15C] .text:000000709EB4F190 EB 17 03 39 STRB W11, [SP,#0x220+var_15B] .text:000000709EB4F194 EA 03 1F 2A MOV W10, WZR .text:000000709EB4F198 EA 1B 03 39 STRB W10, [SP,#0x220+var_15B+1] .text:000000709EB4F19C ED 03 03 91 ADD X13, SP, #0x220+var_160 .text:000000709EB4F1A0 0D 45 00 F9 STR X13, [X8,#0x88] .text:000000709EB4F1A4 0D 45 40 F9 LDR X13, [X8,#0x88] .text:000000709EB4F1A8 0D 41 00 F9 STR X13, [X8,#0x80] .text:000000709EB4F1AC E9 13 00 F9 STR X9, [SP,#0x220+var_200] .text:000000709EB4F1B0 01 00 00 14 B loc_709EB4F1B4 .text:000000709EB4F1B0 .text:000000709EB4F1B4 .text:000000709EB4F1B4 loc_709EB4F1B4 .text:000000709EB4F1B4 E8 53 40 F9 LDR X8, [SP,#0x220+var_180] .text:000000709EB4F1B8 09 45 40 F9 LDR X9, [X8,#0x88] .text:000000709EB4F1BC 2A 01 40 39 LDRB W10, [X9] .text:000000709EB4F1C0 8A 01 00 34 CBZ W10, loc_709EB4F1F0 .text:000000709EB4F1C0 .text:000000709EB4F1C4 01 00 00 14 B loc_709EB4F1C8 .text:000000709EB4F1C4 .text:000000709EB4F1C8 .text:000000709EB4F1C8 loc_709EB4F1C8 .text:000000709EB4F1C8 E8 53 40 F9 LDR X8, [SP,#0x220+var_180] .text:000000709EB4F1CC 09 45 40 F9 LDR X9, [X8,#0x88] .text:000000709EB4F1D0 2A 01 40 39 LDRB W10, [X9] .text:000000709EB4F1D4 4B 7D 04 53 LSR W11, W10, #4 .text:000000709EB4F1D8 4B 1D 1C 33 BFI W11, W10, #4, #8 .text:000000709EB4F1DC 2B 01 00 39 STRB W11, [X9] .text:000000709EB4F1E0 09 45 40 F9 LDR X9, [X8,#0x88] .text:000000709EB4F1E4 29 05 00 91 ADD X9, X9, #1 .text:000000709EB4F1E8 09 45 00 F9 STR X9, [X8,#0x88] .text:000000709EB4F1EC F2 FF FF 17 B loc_709EB4F1B4 .text:000000709EB4F1EC .text:000000709EB4F1F0 .text:000000709EB4F1F0 loc_709EB4F1F0 .text:000000709EB4F1F0 E8 53 40 F9 LDR X8, [SP,#0x220+var_180] .text:000000709EB4F1F4 03 41 40 F9 LDR X3, [X8,#0x80] .text:000000709EB4F1F8 04 05 40 F9 LDR X4, [X8,#8] .text:000000709EB4F1FC E0 1B 40 F9 LDR X0, [SP,#0x220+var_1F0] .text:000000709EB4F200 E1 17 40 F9 LDR X1, [SP,#0x220+var_1F8] .text:000000709EB4F204 E2 13 40 F9 LDR X2, [SP,#0x220+var_200] .text:000000709EB4F208 E0 00 00 94 BL CallVoidMethod_sub_786D1CD588 .text:000000709EB4F208 .text:000000709EB4F20C E0 6B 00 F9 STR X0, [SP,#0x220+var_150] .text:000000709EB4F210 E8 6B 40 F9 LDR X8, [SP,#0x220+var_150] .text:000000709EB4F214 08 01 00 F1 SUBS X8, X8, #0 .text:000000709EB4F218 89 5D 86 52 A9 84+MOV W9, #0x9C2532EC .text:000000709EB4F218 B3 72 .text:000000709EB4F220 AA 61 87 52 4A 30+MOV W10, #0xB9823B0D .text:000000709EB4F220 B7 72 .text:000000709EB4F228 49 01 89 1A CSEL W9, W10, W9, EQ .text:000000709EB4F22C E9 AF 00 B9 STR W9, [SP,#0x220+var_174] .text:000000709EB4F230 E8 0F 00 F9 STR X8, [SP,#0x220+var_208] .text:000000709EB4F234 5C 00 00 14 B loc_709EB4F3A4 .text:000000709EB4F234 .text:000000709EB4F238 .text:000000709EB4F238 loc_709EB4F238 .text:000000709EB4F238 E8 03 1F AA MOV X8, XZR .text:000000709EB4F23C E9 53 40 F9 LDR X9, [SP,#0x220+var_180] .text:000000709EB4F240 28 31 00 F9 STR X8, [X9,#0x60] .text:000000709EB4F244 0A 81 97 52 2A 4C+MOV W10, #0x5A61BC08 .text:000000709EB4F244 AB 72 .text:000000709EB4F24C EA AF 00 B9 STR W10, [SP,#0x220+var_174] .text:000000709EB4F250 55 00 00 14 B loc_709EB4F3A4 .text:000000709EB4F250 .text:000000709EB4F254 .text:000000709EB4F254 loc_709EB4F254 .text:000000709EB4F254 E8 53 40 F9 LDR X8, [SP,#0x220+var_180] .text:000000709EB4F258 00 2D 40 F9 LDR X0, [X8,#0x58] .text:000000709EB4F25C E1 6B 40 F9 LDR X1, [SP,#0x220+var_150] .text:000000709EB4F260 A3 67 00 94 BL GetArrayLength_sub_786D1E70EC .text:000000709EB4F260 .text:000000709EB4F264 E0 BF 00 B9 STR W0, [SP,#0x220+var_164] .text:000000709EB4F268 E0 BF 40 B9 LDR W0, [SP,#0x220+var_164] .text:000000709EB4F26C 00 04 00 11 ADD W0, W0, #1 .text:000000709EB4F270 E1 03 00 2A MOV W1, W0 .text:000000709EB4F274 20 7C 40 93 SXTW X0, W1 ; size .text:000000709EB4F278 26 44 FE 97 BL .malloc .text:000000709EB4F278 .text:000000709EB4F27C E0 5B 00 F9 STR X0, [SP,#0x220+var_170] .text:000000709EB4F280 E0 5B 40 F9 LDR X0, [SP,#0x220+var_170] ; void * .text:000000709EB4F284 E9 BF 40 B9 LDR W9, [SP,#0x220+var_164] .text:000000709EB4F288 29 05 00 11 ADD W9, W9, #1 .text:000000709EB4F28C E1 03 09 2A MOV W1, W9 .text:000000709EB4F290 22 7C 40 93 SXTW X2, W1 ; size_t .text:000000709EB4F294 E9 03 1F 2A MOV W9, WZR .text:000000709EB4F298 E1 03 09 2A MOV W1, W9 ; int .text:000000709EB4F29C E9 17 00 B9 STR W9, [SP,#0x220+var_20C] .text:000000709EB4F2A0 B4 44 FE 97 BL .memset .text:000000709EB4F2A0 .text:000000709EB4F2A4 E8 53 40 F9 LDR X8, [SP,#0x220+var_180] .text:000000709EB4F2A8 02 2D 40 F9 LDR X2, [X8,#0x58] .text:000000709EB4F2AC E1 6B 40 F9 LDR X1, [SP,#0x220+var_150] .text:000000709EB4F2B0 E3 BF 40 B9 LDR W3, [SP,#0x220+var_164] .text:000000709EB4F2B4 E4 5B 40 F9 LDR X4, [SP,#0x220+var_170] .text:000000709EB4F2B8 E0 07 00 F9 STR X0, [SP,#0x220+var_218] .text:000000709EB4F2BC E0 03 02 AA MOV X0, X2 .text:000000709EB4F2C0 E2 17 40 B9 LDR W2, [SP,#0x220+var_20C] .text:000000709EB4F2C4 07 68 00 94 BL GetByteArrayRegion_sub_786D1E72E0 .text:000000709EB4F2C4 .text:000000709EB4F2C8 E9 BF 40 B9 LDR W9, [SP,#0x220+var_164] .text:000000709EB4F2CC E8 53 40 F9 LDR X8, [SP,#0x220+var_180] .text:000000709EB4F2D0 00 21 40 F9 LDR X0, [X8,#0x40] .text:000000709EB4F2D4 09 00 00 B9 STR W9, [X0] .text:000000709EB4F2D8 00 2D 40 F9 LDR X0, [X8,#0x58] .text:000000709EB4F2DC 01 15 40 F9 LDR X1, [X8,#0x28] .text:000000709EB4F2E0 AA 64 00 94 BL DeleteLocalRef_sub_786D1E6588 .text:000000709EB4F2E0 .text:000000709EB4F2E4 E8 53 40 F9 LDR X8, [SP,#0x220+var_180] .text:000000709EB4F2E8 00 2D 40 F9 LDR X0, [X8,#0x58] .text:000000709EB4F2EC 01 11 40 F9 LDR X1, [X8,#0x20] .text:000000709EB4F2F0 A6 64 00 94 BL DeleteLocalRef_sub_786D1E6588 .text:000000709EB4F2F0 .text:000000709EB4F2F4 E8 53 40 F9 LDR X8, [SP,#0x220+var_180] .text:000000709EB4F2F8 00 2D 40 F9 LDR X0, [X8,#0x58] .text:000000709EB4F2FC 01 0D 40 F9 LDR X1, [X8,#0x18] .text:000000709EB4F300 A2 64 00 94 BL DeleteLocalRef_sub_786D1E6588 .text:000000709EB4F300 .text:000000709EB4F304 E8 53 40 F9 LDR X8, [SP,#0x220+var_180] .text:000000709EB4F308 00 2D 40 F9 LDR X0, [X8,#0x58] .text:000000709EB4F30C 01 05 40 F9 LDR X1, [X8,#8] .text:000000709EB4F310 9E 64 00 94 BL DeleteLocalRef_sub_786D1E6588 .text:000000709EB4F310 .text:000000709EB4F314 E8 53 40 F9 LDR X8, [SP,#0x220+var_180] .text:000000709EB4F318 00 2D 40 F9 LDR X0, [X8,#0x58] .text:000000709EB4F31C 01 01 40 F9 LDR X1, [X8] .text:000000709EB4F320 9A 64 00 94 BL DeleteLocalRef_sub_786D1E6588 .text:000000709EB4F320 .text:000000709EB4F324 E8 53 40 F9 LDR X8, [SP,#0x220+var_180] .text:000000709EB4F328 00 2D 40 F9 LDR X0, [X8,#0x58] .text:000000709EB4F32C E1 8F 40 F9 LDR X1, [SP,#0x220+var_108] .text:000000709EB4F330 96 64 00 94 BL DeleteLocalRef_sub_786D1E6588 .text:000000709EB4F330 .text:000000709EB4F334 E8 53 40 F9 LDR X8, [SP,#0x220+var_180] .text:000000709EB4F338 00 2D 40 F9 LDR X0, [X8,#0x58] .text:000000709EB4F33C E1 8B 40 F9 LDR X1, [SP,#0x220+var_113+3] .text:000000709EB4F340 92 64 00 94 BL DeleteLocalRef_sub_786D1E6588 .text:000000709EB4F340 .text:000000709EB4F344 E8 53 40 F9 LDR X8, [SP,#0x220+var_180] .text:000000709EB4F348 00 2D 40 F9 LDR X0, [X8,#0x58] .text:000000709EB4F34C E1 6B 40 F9 LDR X1, [SP,#0x220+var_150] .text:000000709EB4F350 8E 64 00 94 BL DeleteLocalRef_sub_786D1E6588 .text:000000709EB4F350 .text:000000709EB4F354 E8 5B 40 F9 LDR X8, [SP,#0x220+var_170] .text:000000709EB4F358 E0 53 40 F9 LDR X0, [SP,#0x220+var_180] .text:000000709EB4F35C 08 30 00 F9 STR X8, [X0,#0x60] .text:000000709EB4F360 09 81 97 52 29 4C+MOV W9, #0x5A61BC08 .text:000000709EB4F360 AB 72 .text:000000709EB4F368 E9 AF 00 B9 STR W9, [SP,#0x220+var_174] .text:000000709EB4F36C 0E 00 00 14 B loc_709EB4F3A4 .text:000000709EB4F370 .text:000000709EB4F370 loc_709EB4F370 .text:000000709EB4F370 E8 03 1F AA MOV X8, XZR .text:000000709EB4F374 E9 53 40 F9 LDR X9, [SP,#0x220+var_180] .text:000000709EB4F378 28 31 00 F9 STR X8, [X9,#0x60] .text:000000709EB4F37C 0A 81 97 52 2A 4C+MOV W10, #0x5A61BC08 .text:000000709EB4F37C AB 72 .text:000000709EB4F384 EA AF 00 B9 STR W10, [SP,#0x220+var_174] .text:000000709EB4F388 07 00 00 14 B loc_709EB4F3A4 .text:000000709EB4F388 .text:000000709EB4F38C loc_709EB4F38C .text:000000709EB4F38C E8 53 40 F9 LDR X8, [SP,#0x220+var_180] .text:000000709EB4F390 00 31 40 F9 LDR X0, [X8,#0x60] .text:000000709EB4F394 FF 43 08 91 ADD SP, SP, #0x210 .text:000000709EB4F398 FD 7B 41 A9 LDP X29, X30, [SP,#0x10+var_s0] .text:000000709EB4F39C FC 07 42 F8 LDR X28, [SP+0x10+var_10],#0x20 .text:000000709EB4F3A0 C0 03 5F D6 RET .text:000000709EB4F3A0如果本地有存放就读取与设备信息一起上报服务器。 5.2、检测系统环境风险 检测多开: 读取maps查找是否有对应的包名特征 //特征 com.bly.dkplat com.lbe.parallel com.excelliance.dualaid io.va.exposed com.lody.virtual com.qihoo.magic io.virtualapp com.deniu.multi xposed com.android.fcamera com.bly.dkplat com.lbe.parallel com.excelliance.dualaid io.va.exposed com.lody.virtual查找进程中是否有包含关键 xposedbridge libxposed_art.so com.saurik.substrate 5.4、检测magisk 特征 df | grep /sbin/.magisk mount | grep /sbin/.magisk ps | grep magisk strstr /sbin/.magisk /sbin/.magisk5.5、检测自动点击 access /data/data/net.aisence.Touchelper /data/data/com.cyjh.mobileanjian /data/data/com.touchsprite.android cn.testin.itestin com.tencent.wetest com.alibaba.mtl.mdp.kguard com.tencent.wetest.softkeyboard com.baidu.crowdtest.mobileinfo5.6、检测模拟器 access /system/lib/libc_malloc_debug_qemu.so /sys/qemu_trace /system/bin/qemu-props /dev/socket/qemud /dev/qemu_pipe /dev/socket/genyd /dev/socket/baseband_genyd /sys/devices/system/cpu/cpu0/cpufreq/scaling_cur_freq /system/bin/androVM-prop /system/bin/microvirt-prop /system/lib/libdroid4x.so /system/bin/windroyed /system/bin/microvirtd /system/bin/nox-props /system/bin/ttVM-prop /system/bin/droid4x-prop /data/.bluestacks.prop /data/local/tmp/tc/mobileagent /sdcard/.f22 /sdcard/.f22/PhoneInfo.f22 /sdcard/.f22/wxpic /dev/vboxuser /dev/vboxguest /system/bin/genybaseband //查找包名 com.ami.duosupdater.ui com.bluestacks.home com.bluestacks.windowsfilemanager com.bluestacks.settings com.bluestacks.bluestackslocationprovider com.ami.launchmetro com.ami.syncduosservices com.bluestacks.appsettings com.bluestacks.bstfolder com.bluestacks.BstCommandProcessor com.bluestacks.s2p com.kaopu001.tiantianserver __system_property_get init.svc.vbox86-setup init.svc.droid4x init.svc.su_kpbs_daemon init.svc.noxd init.svc.ttVM_x86-setup init.svc.xxkmsg init.svc.microvirtd ro.kernel.android.qemud androVM.vbox_dpi androVM.vbox_graph_mode ro.product.manufacturer persist.phone.id persist.hide_10070 persist.hide_xxxx qemu.sf.fake_camera qemu.sf.lcd_density ro.bootloader init.svc.qemu-props5.7、检测云手机 复制代码 隐藏代码 access getPackageInfo //比较包名 com.haimawan.cloudappstore com.picoo.launcher com.svox.pico com.baidu.mtc.ysera com.baidu.mtc.new_monkey.test com.baidu.crowdtest.mobileinfo cn.testin.itestin5.8、采集设备信息 初始化获取设备信息的类名与对应的方法名 隐藏代码 000000709EDF9090 00 00 00 00 00 00 00 00 05 00 00 00 61 6E 64 72 ............andr 000000709EDF90A0 6F 69 64 2E 74 65 6C 65 70 68 6F 6E 79 2E 54 65 oid.telephony.Te 000000709EDF90B0 6C 65 70 68 6F 6E 79 4D 61 6E 61 67 65 72 00 00 lephonyManager.. 000000709EDF90C0 00 00 00 00 00 00 00 00 00 00 00 00 67 65 74 44 ............getD 000000709EDF90D0 65 76 69 63 65 49 64 00 00 00 00 00 00 00 00 00 eviceId......... 000000709EDF90E0 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 ................ 000000709EDF90F0 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 ................ 000000709EDF9100 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 ................ 000000709EDF9110 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 ................ 000000709EDF9120 00 00 00 00 00 00 00 00 06 00 00 00 61 6E 64 72 ............andr 000000709EDF9130 6F 69 64 2E 74 65 6C 65 70 68 6F 6E 79 2E 54 65 oid.telephony.Te 000000709EDF9140 6C 65 70 68 6F 6E 79 4D 61 6E 61 67 65 72 00 00 lephonyManager.. 000000709EDF9150 00 00 00 00 00 00 00 00 00 00 00 00 67 65 74 56 ............getV 000000709EDF9160 6F 69 63 65 4D 61 69 6C 4E 75 6D 62 65 72 00 00 oiceMailNumber.. 000000709EDF9170 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 ................ 000000709EDF9180 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 ................ 多层反射获取设备信息 复制代码 隐藏代码 双重反射获取设备信息 forName getDeclaredMethod getModifiers .text:000000709EB03C70 62 9E 43 F9 LDR X2, [X19,#0x738] .text:000000709EB03C74 64 3A 43 F9 LDR X4, [X19,#0x670] .text:000000709EB03C78 60 6A 41 F9 LDR X0, [X19,#0x2D0] .text:000000709EB03C7C 61 66 41 F9 LDR X1, [X19,#0x2C8] .text:000000709EB03C80 63 EA 41 F9 LDR X3, [X19,#0x3D0] .text:000000709EB03C84 68 62 01 F9 STR X8, [X19,#0x2C0] .text:000000709EB03C88 69 5E 01 F9 STR X9, [X19,#0x2B8] .text:000000709EB03C8C 6A 5A 01 F9 STR X10, [X19,#0x2B0] .text:000000709EB03C90 6B AE 02 B9 STR W11, [X19,#0x2AC] .text:000000709EB03C94 6C AA 02 B9 STR W12, [X19,#0x2A8]其它设备信息: 在跳出VM的Hadnle处下断点即可分析出获取其它的设备信息。 5.9、VM加密设备信息 每获取一次设备信息加密一次,在VM中执行对应Handle加密。 复制代码 隐藏代码 .text000000709EA93920 A8 02 40 B9 LDR W8, [X21] .text:000000709EA93924 98 02 40 F9 LDR X24, [X20] .text:000000709EA93928 09 91 03 51 SUB W9, W8, #0xE4 .text:000000709EA9392C 0A F1 01 51 SUB W10, W8, #0x7C ; '|' .text:000000709EA93930 3F 81 00 71 CMP W9, #0x20 ; ' ' .text:000000709EA93934 48 31 88 1A CSEL W8, W10, W8, CC .text:000000709EA93938 09 1D 03 51 SUB W9, W8, #0xC7 .text:000000709EA9393C 3F 71 00 71 CMP W9, #0x1C .text:000000709EA93940 A8 00 00 54 B.HI loc_709EA93954 .text:000000709EA93940 .text:000000709EA93944 C8 4E 29 8B ADD X8, X22, W9,UXTW#3 .text:000000709EA93948 08 21 40 F9 LDR X8, [X8,#0x40] ; 值的基址,取值 .text:000000709EA9394C 08 03 00 F9 STR X8, [X24] ; 存值 .text:000000709EA93950 37 00 00 14 B loc_709EA93A2C 六、加密流程分析6.1、压缩设备数据 计算设备信息CRC与设备数据组合 复制代码 隐藏代码 .text:000000709EB765F8 EncData_sub_70576365F8 .text:000000709EB765F8 ; __unwind { // 1000 .text:000000709EB765F8 28 7A AB 52 A8 32+MOV W8, #0x5BD1E995 .text:000000709EB765F8 9D 72 .text:000000709EB76600 49 00 01 4A EOR W9, W2, W1 .text:000000709EB76604 2A 10 00 71 SUBS W10, W1, #4 .text:000000709EB76608 E3 01 00 54 B.CC loc_709EB76644 .text:000000709EB76608 .text:000000709EB7660C 4B 75 1E 12 AND W11, W10, #0xFFFFFFFC .text:000000709EB76610 6C 11 00 91 ADD X12, X11, #4 .text:000000709EB76614 ED 03 00 AA MOV X13, X0 .text:000000709EB76614 .text:000000709EB76618 .text:000000709EB76618 loc_709EB76618 .text:000000709EB76618 AE 45 40 B8 LDR W14, [X13],#4 .text:000000709EB7661C 29 7D 08 1B MUL W9, W9, W8 .text:000000709EB76620 21 10 00 51 SUB W1, W1, #4 .text:000000709EB76624 CE 7D 08 1B MUL W14, W14, W8 .text:000000709EB76628 CE 61 4E 4A EOR W14, W14, W14,LSR#24 .text:000000709EB7662C CE 7D 08 1B MUL W14, W14, W8 .text:000000709EB76630 C9 01 09 4A EOR W9, W14, W9 .text:000000709EB76634 3F 0C 00 71 CMP W1, #3 .text:000000709EB76638 08 FF FF 54 B.HI loc_709EB76618 .text:000000709EB76638 .text:000000709EB7663C 41 01 0B 4B SUB W1, W10, W11 .text:000000709EB76640 00 00 0C 8B ADD X0, X0, X12 .text:000000709EB76640 .text:000000709EB76644 .text:000000709EB76644 loc_709EB76644 .text:000000709EB76644 3F 04 00 71 CMP W1, #1 .text:000000709EB76648 20 01 00 54 B.EQ loc_709EB7666C .text:000000709EB76648 .text:000000709EB7664C 3F 08 00 71 CMP W1, #2 .text:000000709EB76650 A0 00 00 54 B.EQ loc_709EB76664 .text:000000709EB76650 .text:000000709EB76654 3F 0C 00 71 CMP W1, #3 .text:000000709EB76658 01 01 00 54 B.NE loc_709EB76678 .text:000000709EB76658 .text:000000709EB7665C 0A 08 40 39 LDRB W10, [X0,#2] .text:000000709EB76660 29 41 0A 4A EOR W9, W9, W10,LSL#16 .text:000000709EB76660 .text:000000709EB76664 .text:000000709EB76664 loc_709EB76664 .text:000000709EB76664 0A 04 40 39 LDRB W10, [X0,#1] .text:000000709EB76668 29 21 0A 4A EOR W9, W9, W10,LSL#8 .text:000000709EB76668 .text:000000709EB7666C .text:000000709EB7666C loc_709EB7666C .text:000000709EB7666C 0A 00 40 39 LDRB W10, [X0] .text:000000709EB76670 49 01 09 4A EOR W9, W10, W9 .text:000000709EB76674 29 7D 08 1B MUL W9, W9, W8 .text:000000709EB76674 .text:000000709EB76678 .text:000000709EB76678 loc_709EB76678 .text:000000709EB76678 29 35 49 4A EOR W9, W9, W9,LSR#13 .text:000000709EB7667C 28 7D 08 1B MUL W8, W9, W8 .text:000000709EB76680 00 3D 48 4A EOR W0, W8, W8,LSR#15 .text:000000709EB76684 C0 03 5F D6 RET压缩组合后设备数据 复制代码 隐藏代码 __int64 __fastcall sub_705762D9DC(__int64 a1, _QWORD *a2, __int64 a3, __int64 a4, unsigned int a5) { int v5; // w8 int v6; // w0 int v7; // w0 int v8; // w11 unsigned int v10; // [xsp+54h] [xbp-CCh] int i; // [xsp+58h] [xbp-C8h] unsigned int v12; // [xsp+5Ch] [xbp-C4h] __int64 v13; // [xsp+60h] [xbp-C0h] BYREF int v14; // [xsp+68h] [xbp-B8h] __int64 v15; // [xsp+78h] [xbp-A8h] unsigned int v16; // [xsp+80h] [xbp-A0h] __int64 v17; // [xsp+88h] [xbp-98h] __int64 v18; // [xsp+A0h] [xbp-80h] __int64 v19; // [xsp+A8h] [xbp-78h] __int64 v20; // [xsp+B0h] [xbp-70h] unsigned int v21; // [xsp+D4h] [xbp-4Ch] __int64 v22; // [xsp+D8h] [xbp-48h] __int64 v23; // [xsp+E0h] [xbp-40h] _QWORD *v24; // [xsp+E8h] [xbp-38h] __int64 v25; // [xsp+F0h] [xbp-30h] unsigned int v26; // [xsp+FCh] [xbp-24h] __int64 v27; // [xsp+100h] [xbp-20h] __int64 v28; // [xsp+108h] [xbp-18h] v25 = a1; v24 = a2; v23 = a3; v22 = a4; v21 = a5; v13 = a3; v14 = a4; v15 = a1; v16 = *a2; v27 = v16; v28 = *a2; for ( i = 1425515106; ; i = 2121135395 ) { while ( 1 ) { while ( 1 ) { while ( 1 ) { while ( 1 ) { while ( 1 ) { while ( 1 ) { while ( 1 ) { while ( 1 ) { while ( i == 1425515106 ) { if ( v27 == v28 ) v5 = 1946294605; else v5 = 711699392; i = v5; } if ( i != 711699392 ) break; v26 = -5; i = 2121135395; } if ( i != 1946294605 ) break; v18 = 0LL; v19 = 0LL; v20 = 0LL; v12 = sub_709EB6DFD8(&v13, v21, "2.3.3", 112LL); if ( v12 ) v6 = 1708398168; else v6 = -1398807773; i = v6; } if ( i != 1708398168 ) break; v26 = v12; i = 2121135395; } if ( i != -1398807773 ) break; v12 = sub_709EB6ECDC(&v13, 4LL); if ( v12 == 1 ) v7 = 1641238281; else v7 = -1560729400; i = v7; } if ( i != -1560729400 ) break; sub_709EB6E244(&v13); if ( v12 ) v8 = -1477061934; else v8 = -1711647064; i = v8; } if ( i != -1711647064 ) break; i = 584363032; v10 = -5; } if ( i != -1477061934 ) break; i = 584363032; v10 = v12; } if ( i != 584363032 ) break; v26 = v10; i = 2121135395; } if ( i != 1641238281 ) break; *v24 = v17; v12 = sub_709EB6E244(&v13); v26 = v12; } return v26; }6.2、生成AES KEY IV 随机数组合生成AES KEY IV 复制代码 隐藏代码 gettimeofday srand .text:000000709EB328A0 sprintf_sub_70575F28A0 .text:000000709EB328A0 .text:000000709EB328A0 var_24= -0x24 .text:000000709EB328A0 format= -0x20 .text:000000709EB328A0 s= -0x18 .text:000000709EB328A0 var_10= -0x10 .text:000000709EB328A0 .text:000000709EB328A0 ; __unwind { // 1000 .text:000000709EB328A0 FF C3 00 D1 SUB SP, SP, #0x30 .text:000000709EB328A4 FE 13 00 F9 STR X30, [SP,#0x30+var_10] .text:000000709EB328A8 E0 0F 00 F9 STR X0, [SP,#0x30+s] .text:000000709EB328AC E1 0B 00 F9 STR X1, [SP,#0x30+format] .text:000000709EB328B0 E2 0F 00 B9 STR W2, [SP,#0x30+var_24] .text:000000709EB328B4 E0 0F 40 F9 LDR X0, [SP,#0x30+s] ; s .text:000000709EB328B8 E1 0B 40 F9 LDR X1, [SP,#0x30+format] ; format .text:000000709EB328BC E2 0F 40 B9 LDR W2, [SP,#0x30+var_24] .text:000000709EB328C0 98 B6 FE 97 BL .sprintf .text:000000709EB328C0 .text:000000709EB328C4 FE 13 40 F9 LDR X30, [SP,#0x30+var_10] .text:000000709EB328C8 FF C3 00 91 ADD SP, SP, #0x30 ; '0' .text:000000709EB328CC C0 03 5F D6 RET //生成随机数AES KEY IV fda958f6-07e5-47 KEY e4ae2f7b-96b5-4a IV6.3、RSA加密AES KEY IV 将随机数AES KEY IV组合成一个字符串fda958f6-07e5-47e4ae2f7b-96b5-4a,RSA私钥加密该字符串。 RSA私钥:(隐去部分) 复制代码 隐藏代码 MIICeAIBADANBgkqhkiG9w0BAQEFAASCAmIwggJeAgEAAoGBALE2OfQ8BYg9Lq4nKGTamXyia6raCc1adzCOsFrnk/VN0s2W8yQJfYdq+QUNRHv0zANW0Uafh7nHCWeBn/GOC26xTsUku3/ElECGthT5ED0MOO8EQ6dhci4So/Y/fNuAczqDFk5RKRbmo1gz7xuCdUTQYmD+h1cjl95HGrY6TMinAgMBAAECgYBCHYwjvh0GRmVbHkrozdID+QkYdj6/+eeMG0BauhmupLlocNAH+u51joiXxOpvINbYzBRKOAzIWCT/FBKbabaDl5IhuUwV+CJ90SBLAbs/Wd+QjnUhXbyKb+Tm3+Uz2y26xWc7XdhGNe3Wjyz2+fN8CbfdC2SlUnibADOEQXJFIQJBAOUgSH/+uyIJKo6DOHJSfrhDlYX875H4Yq8ifuS1R7hQcK5T8sYV/OIzTRSvFaYL+FG8nA9vr8rulojcDPYzqrcCQQDF/yuUtb1wliR+zH7iE/5pv0dGfuwhSec777TYuLEP6VnX68zI/Kyq2JdIYYO7MidjH4bFd50NnRacHi3AtKGRAkEAiU+Gg0Y6CVSq70sOSdzMWksOUYTaYYUURtaKay+Ecp2qWZ6vkCxfJ4QM/odKlv73aqx4bfvFwvymtBADqIwgEwJBAIHtZq3ZbQz6mcxTaVf2Atdl2+HY3B8kHgdoz2YAHMDyQjC83c9ub+hU5UFsLEOlL8+OGqRuT7NlSDb+Xsu8POECQQDPcNOysMNbrLh1mGe6ydUsojSbheAIOZPQ/lhUbhzPXAXTYaPkTq7uty6SYZOMtWLxIFZ1eA9HHm3tJOCgC888反射调用JAVA加密: 复制代码 隐藏代码 .text:000000709EB328D0 decode_sub_70575F28D0 .text:000000709EB328D0 .text:000000709EB328D0 var_3C= -0x3C .text:000000709EB328D0 var_38= -0x38 .text:000000709EB328D0 var_30= -0x30 .text:000000709EB328D0 var_28= -0x28 .text:000000709EB328D0 var_20= -0x20 .text:000000709EB328D0 var_18= -0x18 .text:000000709EB328D0 var_10= -0x10 .text:000000709EB328D0 .text:000000709EB328D0 ; __unwind { // 1000 .text:000000709EB328D0 FF 03 01 D1 SUB SP, SP, #0x40 .text:000000709EB328D4 FE 1B 00 F9 STR X30, [SP,#0x40+var_10] .text:000000709EB328D8 E0 17 00 F9 STR X0, [SP,#0x40+var_18] .text:000000709EB328DC E1 13 00 F9 STR X1, [SP,#0x40+var_20] .text:000000709EB328E0 E2 0F 00 F9 STR X2, [SP,#0x40+var_28] .text:000000709EB328E4 E3 0B 00 F9 STR X3, [SP,#0x40+var_30] .text:000000709EB328E8 E4 07 00 F9 STR X4, [SP,#0x40+var_38] .text:000000709EB328EC E5 07 00 B9 STR W5, [SP,#0x40+var_3C] .text:000000709EB328F0 E0 17 40 F9 LDR X0, [SP,#0x40+var_18] .text:000000709EB328F4 E1 13 40 F9 LDR X1, [SP,#0x40+var_20] .text:000000709EB328F8 E2 0F 40 F9 LDR X2, [SP,#0x40+var_28] .text:000000709EB328FC E3 0B 40 F9 LDR X3, [SP,#0x40+var_30] .text:000000709EB32900 E4 07 40 F9 LDR X4, [SP,#0x40+var_38] .text:000000709EB32904 E5 07 40 B9 LDR W5, [SP,#0x40+var_3C] .text:000000709EB32908 2B 83 00 94 BL CallObjectMethod_sub_786D1D15B4 .text:000000709EB32908 .text:000000709EB3290C FE 1B 40 F9 LDR X30, [SP,#0x40+var_10] .text:000000709EB32910 FF 03 01 91 ADD SP, SP, #0x40 ; '@' .text:000000709EB32914 C0 03 5F D6 RET .text:000000709EB32958 getInstance_sub_70575F2958 .text:000000709EB32958 .text:000000709EB32958 var_38= -0x38 .text:000000709EB32958 var_30= -0x30 .text:000000709EB32958 var_28= -0x28 .text:000000709EB32958 var_20= -0x20 .text:000000709EB32958 var_18= -0x18 .text:000000709EB32958 var_10= -0x10 .text:000000709EB32958 .text:000000709EB32958 ; __unwind { // 1000 .text:000000709EB32958 FF 03 01 D1 SUB SP, SP, #0x40 .text:000000709EB3295C FE 1B 00 F9 STR X30, [SP,#0x40+var_10] .text:000000709EB32960 E0 17 00 F9 STR X0, [SP,#0x40+var_18] .text:000000709EB32964 E1 13 00 F9 STR X1, [SP,#0x40+var_20] .text:000000709EB32968 E2 0F 00 F9 STR X2, [SP,#0x40+var_28] .text:000000709EB3296C E3 0B 00 F9 STR X3, [SP,#0x40+var_30] .text:000000709EB32970 E4 07 00 F9 STR X4, [SP,#0x40+var_38] .text:000000709EB32974 E0 17 40 F9 LDR X0, [SP,#0x40+var_18] .text:000000709EB32978 E1 13 40 F9 LDR X1, [SP,#0x40+var_20] .text:000000709EB3297C E2 0F 40 F9 LDR X2, [SP,#0x40+var_28] .text:000000709EB32980 E3 0B 40 F9 LDR X3, [SP,#0x40+var_30] .text:000000709EB32984 E4 07 40 F9 LDR X4, [SP,#0x40+var_38] .text:000000709EB32988 0B 83 00 94 BL CallObjectMethod_sub_786D1D15B4 .text:000000709EB32988 .text:000000709EB3298C FE 1B 40 F9 LDR X30, [SP,#0x40+var_10] .text:000000709EB32990 FF 03 01 91 ADD SP, SP, #0x40 ; '@' .text:000000709EB32994 C0 03 5F D6 RET .text:000000709EB32998 generatePrivate_sub_70575F2998 .text:000000709EB32998 .text:000000709EB32998 var_38= -0x38 .text:000000709EB32998 var_30= -0x30 .text:000000709EB32998 var_28= -0x28 .text:000000709EB32998 var_20= -0x20 .text:000000709EB32998 var_18= -0x18 .text:000000709EB32998 var_10= -0x10 .text:000000709EB32998 .text:000000709EB32998 ; __unwind { // 1000 .text:000000709EB32998 FF 03 01 D1 SUB SP, SP, #0x40 .text:000000709EB3299C FE 1B 00 F9 STR X30, [SP,#0x40+var_10] .text:000000709EB329A0 E0 17 00 F9 STR X0, [SP,#0x40+var_18] .text:000000709EB329A4 E1 13 00 F9 STR X1, [SP,#0x40+var_20] .text:000000709EB329A8 E2 0F 00 F9 STR X2, [SP,#0x40+var_28] .text:000000709EB329AC E3 0B 00 F9 STR X3, [SP,#0x40+var_30] .text:000000709EB329B0 E4 07 00 F9 STR X4, [SP,#0x40+var_38] .text:000000709EB329B4 E0 17 40 F9 LDR X0, [SP,#0x40+var_18] .text:000000709EB329B8 E1 13 40 F9 LDR X1, [SP,#0x40+var_20] .text:000000709EB329BC E2 0F 40 F9 LDR X2, [SP,#0x40+var_28] .text:000000709EB329C0 E3 0B 40 F9 LDR X3, [SP,#0x40+var_30] .text:000000709EB329C4 E4 07 40 F9 LDR X4, [SP,#0x40+var_38] .text:000000709EB329C8 B5 7C 00 94 BL calljavamethond_sub_786D1CFC9C .text:000000709EB329C8 .text:000000709EB329CC FE 1B 40 F9 LDR X30, [SP,#0x40+var_10] .text:000000709EB329D0 FF 03 01 91 ADD SP, SP, #0x40 ; '@' .text:000000709EB329D4 C0 03 5F D6 RET .text:000000709EB32A60 doFinal_sub_70575F2A60 .text:000000709EB32A60 .text:000000709EB32A60 var_38= -0x38 .text:000000709EB32A60 var_30= -0x30 .text:000000709EB32A60 var_28= -0x28 .text:000000709EB32A60 var_20= -0x20 .text:000000709EB32A60 var_18= -0x18 .text:000000709EB32A60 var_10= -0x10 .text:000000709EB32A60 .text:000000709EB32A60 ; __unwind { // 1000 .text:000000709EB32A60 FF 03 01 D1 SUB SP, SP, #0x40 .text:000000709EB32A64 FE 1B 00 F9 STR X30, [SP,#0x40+var_10] .text:000000709EB32A68 E0 17 00 F9 STR X0, [SP,#0x40+var_18] .text:000000709EB32A6C E1 13 00 F9 STR X1, [SP,#0x40+var_20] .text:000000709EB32A70 E2 0F 00 F9 STR X2, [SP,#0x40+var_28] .text:000000709EB32A74 E3 0B 00 F9 STR X3, [SP,#0x40+var_30] .text:000000709EB32A78 E4 07 00 F9 STR X4, [SP,#0x40+var_38] .text:000000709EB32A7C E0 17 40 F9 LDR X0, [SP,#0x40+var_18] .text:000000709EB32A80 E1 13 40 F9 LDR X1, [SP,#0x40+var_20] .text:000000709EB32A84 E2 0F 40 F9 LDR X2, [SP,#0x40+var_28] .text:000000709EB32A88 E3 0B 40 F9 LDR X3, [SP,#0x40+var_30] .text:000000709EB32A8C E4 07 40 F9 LDR X4, [SP,#0x40+var_38] .text:000000709EB32A90 83 7C 00 94 BL calljavamethond_sub_786D1CFC9C .text:000000709EB32A90 .text:000000709EB32A94 FE 1B 40 F9 LDR X30, [SP,#0x40+var_10] .text:000000709EB32A98 FF 03 01 91 ADD SP, SP, #0x40 ; '@' .text:000000709EB32A9C C0 03 5F D6 RETRSA私钥加密后的AES KEY IV: 复制代码 隐藏代码 00000000 98 93 1B 85 66 82 76 26 88 2B 09 13 AA 22 4E 76 00000020 9B 3F 47 93 8B A7 CD D7 A6 48 3D C9 70 55 29 6A 00000040 57 B7 65 AE F4 3E 2C CB 5C E1 CD 6B 57 B5 86 2F 00000060 1D 81 FC A3 56 27 64 13 27 42 A0 84 C3 23 CD 0D 00000080 05 D1 0D B0 22 36 FE 36 B5 17 61 6F 19 14 1D B1 00000100 67 A0 1F F4 F2 09 83 CA C1 9A C4 64 14 F4 54 7D 00000120 DA6.4、AES加密压缩后设备数据 用随机数生成的KEY加密压缩后的设备数据: 复制代码 隐藏代码 // X0:key,x1:长度,X2:返回值 __int64 __fastcall AES_initkey_sub_70576377C8(unsigned int *a1, int a2, unsigned int *a3) { unsigned int v3; // w8 unsigned int v29; // w17 v3 = -1; if ( a1 && a3 ) { if ( a2 != 128 && a2 != 256 && a2 != 192 ) return 4294967294LL; if ( a2 == 128 ) { v4 = 10; } else if ( a2 == 192 ) { v4 = 12; } else { v4 = 14; } a3[60] = v4; v6 = _byteswap_ulong(*a1); *a3 = v6; a3[1] = _byteswap_ulong(a1[1]); a3[2] = _byteswap_ulong(a1[2]); a3[3] = _byteswap_ulong(a1[3]); if ( a2 == 128 ) { v7 = 0LL; v8 = a3 + 4; do { v9 = *(v8 - 1); v6 ^= dword_709EBD4F74[BYTE2(v9)] & 0xFF000000 ^ dword_709EBD5374[BYTE1(v9)] & 0xFF0000 ^ dword_709EBD5774[(unsigned __int8)v9] & 0xFF00 ^ byte_709EBD5B74[4 * HIBYTE(v9)] ^ *(_DWORD *)((char *)&unk_709EBD5F74 + v7); v10 = *(v8 - 2); v7 += 4LL; v11 = *(v8 - 3) ^ v6; *v8 = v6; v8[1] = v11; v12 = v10 ^ v11; v8[2] = v12; v8[3] = v9 ^ v12; v8 += 4; } while ( v7 != 40 ); } else { a3[4] = _byteswap_ulong(a1[4]); a3[5] = _byteswap_ulong(a1[5]); if ( a2 == 192 ) { v13 = 0LL; for ( i = a3 + 6; ; i += 6 ) { v16 = *(i - 1); v6 ^= dword_709EBD4F74[BYTE2(v16)] & 0xFF000000 ^ dword_709EBD5374[BYTE1(v16)] & 0xFF0000 ^ dword_709EBD5774[(unsigned __int8)v16] & 0xFF00 ^ byte_709EBD5B74[4 * HIBYTE(v16)] ^ *(_DWORD *)((char *)&unk_709EBD5F74 + v13); v17 = *(i - 3); v18 = *(i - 5) ^ v6; v19 = *(i - 4) ^ v18; *i = v6; i[1] = v18; i[2] = v19; i[3] = v17 ^ v19; if ( v13 == 28 ) break; v13 += 4LL; v15 = *(i - 2) ^ v17 ^ v19; i[4] = v15; i[5] = v16 ^ v15; } } else { a3[6] = _byteswap_ulong(a1[6]); a3[7] = _byteswap_ulong(a1[7]); v20 = 0LL; for ( j = a3 + 8; ; j += 8 ) { v25 = *(j - 1); v6 ^= dword_709EBD4F74[BYTE2(v25)] & 0xFF000000 ^ dword_709EBD5374[BYTE1(v25)] & 0xFF0000 ^ dword_709EBD5774[(unsigned __int8)v25] & 0xFF00 ^ byte_709EBD5B74[4 * HIBYTE(v25)] ^ *(_DWORD *)((char *)&unk_709EBD5F74 + v20); v26 = *(j - 5); v27 = *(j - 7) ^ v6; v28 = *(j - 6) ^ v27; *j = v6; j[1] = v27; j[2] = v28; j[3] = v26 ^ v28; if ( v20 == 24 ) break; v29 = v26 ^ v28; v22 = dword_709EBD4F74[HIBYTE(v29)] & 0xFF000000 ^ *(j - 4) ^ dword_709EBD5374[BYTE2(v29)] & 0xFF0000 ^ dword_709EBD5774[BYTE1(v29)] & 0xFF00 ^ byte_709EBD5B74[4 * (unsigned __int8)v29]; v23 = *(j - 2); v24 = *(j - 3) ^ v22; j[4] = v22; j[5] = v24; v20 += 4LL; j[6] = v23 ^ v24; j[7] = v25 ^ v23 ^ v24; } } } return 0; } return v3; } // X0:原数据,X1:返回,x2:大小,x3:初始化后key,x4:IV long double __fastcall AES_enc_data_sub_705760C380( _QWORD *a1, long double *a2, unsigned __int64 a3, __int64 a4, long double *a5, void (__fastcall *a6)(long double *, long double *, __int64)) { unsigned __int64 v6; // x24 unsigned __int64 v10; // x8 unsigned __int64 v11; // x22 unsigned __int64 v12; // x27 long double *v13; // x26 unsigned __int64 v14; // x19 long double *v15; // x8 _QWORD *v16; // x28 long double *v17; // x25 long double *v18; // x8 __int64 v19; // x24 unsigned __int64 v20; // x25 _QWORD *v21; // x22 long double *v22; // x10 unsigned __int64 v23; // x27 unsigned __int64 v24; // x10 unsigned __int64 v25; // x13 __int128 v26; // q0 __int128 v27; // q1 _OWORD *v28; // x14 unsigned __int64 v29; // x9 __int64 v30; // x14 long double *v31; // x23 __int64 v32; // x13 __int64 v33; // x15 unsigned __int64 v34; // x10 __int64 v35; // x11 long double *v36; // x17 unsigned __int64 v37; // x14 unsigned __int64 v38; // x13 int8x16_t v39; // q0 int8x16_t v40; // q1 int8x16_t v41; // q2 int8x16_t v42; // q3 int8x16_t *v43; // x15 unsigned __int64 v44; // x11 unsigned __int64 v45; // x12 long double result; // q0 _QWORD *v48; // [xsp+8h] [xbp-58h] _QWORD *v49; // [xsp+8h] [xbp-58h] v6 = a3; v10 = a3 - 16; if ( a3 < 0x10 ) { v18 = a5; v13 = a2; v14 = a3; } else { v11 = v10 & 0xFFFFFFFFFFFFFFF0LL; v12 = (v10 & 0xFFFFFFFFFFFFFFF0LL) + 16; v13 = (long double *)((char *)a2 + v12); v14 = v10 - (v10 & 0xFFFFFFFFFFFFFFF0LL); v15 = a5; v16 = a1; v17 = a2; v48 = a1; do { *(_QWORD *)v17 = *(_QWORD *)v15 ^ *v16; *((_QWORD *)v17 + 1) = *((_QWORD *)v15 + 1) ^ v16[1]; a6(v17, v17, a4); v6 -= 16LL; v15 = v17++; v16 += 2; } while ( v6 > 0xF ); v18 = (long double *)((char *)a2 + v11); a1 = (_QWORD *)((char *)v48 + v12); } if ( v14 ) { v19 = 0LL; v20 = -(__int64)v14; v21 = a1; v22 = v13; v23 = v14; v49 = a1; while ( 1 ) { v30 = 2 * v19; v29 = 0LL; v31 = v22; if ( v20 = v2_1.length) { break; } String v5 = v2_1[v4]; if(!v5.startsWith("XXID")) { ++v4; goto label_76; } String v5_1 = v5.substring(5, v5.length()); if(TextUtils.isEmpty(v5_1)) { ++v4; goto label_76; } FMAgent.xxid = v5_1; break; } } ++v1; } } } } catch(Exception v10_1) { v10_1.printStackTrace(); } goto label_99; ++v4; goto label_76; ++v1; goto label_60; label_99: InputStream v9_2 = v9.getInputStream(); BufferedReader v10_4 = new BufferedReader(new InputStreamReader(v9_2, "utf-8")); StringBuilder v12_1 = new StringBuilder(); while(true) { String v0 = v10_4.readLine(); if(v0 == null) { break; } v12_1.append(v0); } v9_2.close(); v11.close(); return v12_1.toString(); }成功后服务器返回blackbox: 复制代码 隐藏代码 {"code":"000","desc":"k9OCtUBncUi1/r3N84z30FFW3AwxnmZnJfuKa2bhCcS/s9mKZAuBFnJ6BYRDDpUkz+fxJhWvD+bbun3eUbCyiw=="}这个值是根据硬件ID,OAID、文件ID生成。 七、加密漏洞还原与中人间攻击过程7.1、通过私钥解析出公钥 理论上我们很难从私钥(只有d,n)中推导公钥的,也无法通过公钥推导出私钥,但是该SDK使用了私钥为PKCS编码格式,该私钥数据可以按如下结构进行解析: 复制代码 隐藏代码 RSAPrivateKey ::= SEQUENCE { versionVersion, modulusINTEGER, -- n publicExponentINTEGER, -- e privateExponentINTEGER, -- d prime1INTEGER, -- p prime2INTEGER, -- q exponent1INTEGER, -- d mod (p-1) exponent2INTEGER, -- d mod (q-1) coefficientINTEGER, -- (inverse of q) mod p otherPrimeInfosOtherPrimeInfos OPTIONAL }从结构中可以看出私钥其实是含有生成密钥对的p和q以及公私钥对(e,n)。通过私钥格式分析可以分析出公钥数据,用代码实现如下: 加载私钥: 复制代码 隐藏代码 /** * 从字符串中获取私钥 * home.php?mod=space&uid=952169 privateKeyStr * @return * @throws Exception */ public static RSAPrivateKey loadPrivateKeyByStr(String privateKeyStr) throws Exception { try { byte[] buffer = java.util.Base64.getDecoder().decode(privateKeyStr); PKCS8EncodedKeySpec keySpec = new PKCS8EncodedKeySpec(buffer); KeyFactory keyFactory = KeyFactory.getInstance("RSA"); return (RSAPrivateKey) keyFactory.generatePrivate(keySpec); } catch (NoSuchAlgorithmException e) { throw new Exception("无此算法"); } catch (InvalidKeySpecException e) { throw new Exception("私钥非法"); } catch (NullPointerException e) { throw new Exception("私钥数据为空"); } } public static String gethexPublicKey(String modulus, String exponent) { try { BigInteger b1 = new BigInteger(modulus,16); //此处为进制数 BigInteger b2 = new BigInteger(exponent,16); KeyFactory keyFactory = KeyFactory.getInstance("RSA"); RSAPublicKeySpec keySpec = new RSAPublicKeySpec(b1, b2); RSAPublicKey publicKey = (RSAPublicKey) keyFactory.generatePublic(keySpec); String publicKeyString = Base64.encode(publicKey.getEncoded()); return publicKeyString; } catch (Exception e) { e.printStackTrace(); return null; } }解析出公钥: 复制代码 隐藏代码 //从SDK中的私钥解析出公钥(隐去部分) String strprivatekey = "MIICeAIBADANBgkqhkiG9w0BAQEFAASCAmIwggJeAgEAAoGBALE2OfQ8BYg9Lq4nKGTamXyia6raCc1adzCOsFrnk/VN0s2W8yQJfYdq+QUNRHv0zANW0Uafh7nHCWeBn/GOC26xTsUku3/ElECGthT5ED0MOO8EQ6dhci4So/Y/fNuAczqDFk5RKRbmo1gz7xuCdUTQYmD+h1cjl95HGrY6TMinAgMBAAECgYBCHYwjvh0GRmVbHkrozdID+QkYdj6/+eeMG0BauhmupLlocNAH+u51joiXxOpvINbYzBRKOAzIWCT/FBKbabaDl5IhuUwV+CJ90SBLAbs/Wd+QjnUhXbyKb+Tm3+Uz2y26xWc7XdhGNe3Wjyz2+fN8CbfdC2SlUnibADOEQXJFIQJBAOUgSH/+uyIJKo6DOHJSfrhDlYX875H4Yq8ifuS1R7hQcK5T8sYV/OIzTRSvFaYL+FG8nA9vr8rulojcDPYzqrcCQQDF/yuUtb1wliR+zH7iE/5pv0dGfuwhSec777TYuLEP6VnX68zI/Kyq2JdIYYO7MidjH4bFd50NnRacHi3AtKGRAkEAiU+Gg0Y6CVSq70sOSdzMWksOUYTaYYUURtaKay+Ecp2qWZ6vkCxfJ4QM/odKlv73aqx4bfvFwvymtBADqIwgEwJBAIHtZq3ZbQz6mcxTaVf2Atdl2+HY3B8kHgdoz2YAHMDyQjC83c9ub+hU5UFsLEOlL8+OGqRuT7NlSDb+Xsu8POECQQDPcNOysMNbrLh1mGe6ydUsojSbheAIOZPQ/lhUbhzPXAXTYaPkTq7uty6SYZOMtWLxIFZ1eA9HHm3tJOCgC888"; RSAPrivateKey privateKey = RSAUtils.loadPrivateKeyByStr(strprivatekey); // 得到公钥 BigInteger modulus = privateKey.getModulus(); byte[] bmodulus = modulus.toByteArray(); String modulusString = StringToHex.bytesToHex(bmodulus); System.out.println("modulusString:"+modulusString); String publicKeyString = RSAEncrypt.gethexPublicKey(modulusString, "010001"); System.out.println("publicKeyString:"+publicKeyString);7.2、公钥解密出AES KEY IV 得到公钥后做解密测试,只要能把上报到服务器端的请求体中加密的AES KEY IV解密出来就能解出AES加密的设备数据。 复制代码 隐藏代码 //私钥加密的AES KEY IV byte[] keydata = { (byte)0x98, (byte)0x93, 0x1B, (byte)0x85, 0x66, (byte)0x82, 0x76, 0x26, (byte)0x88, 0x2B, 0x09, 0x13, (byte)0xAA, 0x22, 0x4E, 0x76, (byte)0x9B, 0x3F, 0x47, (byte)0x93, (byte)0x8B, (byte)0xA7, (byte)0xCD, (byte)0xD7, (byte)0xA6, 0x48, 0x3D, (byte)0xC9, 0x70, 0x55, 0x29, 0x6A, 0x57, (byte)0xB7, 0x65, (byte)0xAE, (byte)0xF4, 0x3E, 0x2C, (byte)0xCB, 0x5C, (byte)0xE1, (byte)0xCD, 0x6B, 0x57, (byte)0xB5, (byte)0x86, 0x2F, 0x1D, (byte)0x81, (byte)0xFC, (byte)0xA3, 0x56, 0x27, 0x64, 0x13, 0x27, 0x42, (byte)0xA0, (byte)0x84, (byte)0xC3, 0x23, (byte)0xCD, 0x0D, 0x05, (byte)0xD1, 0x0D, (byte)0xB0, 0x22, 0x36, (byte)0xFE, 0x36, (byte)0xB5, 0x17, 0x61, 0x6F, 0x19, 0x14, 0x1D, (byte)0xB1, 0x67, (byte)0xA0, 0x1F, (byte)0xF4, (byte)0xF2, 0x09, (byte)0x83, (byte)0xCA, (byte)0xC1, (byte)0x9A, (byte)0xC4, 0x64, 0x14, (byte)0xF4, 0x54, 0x7D, (byte)0xDA, 0x3A, 0x40, 0x75, 0x28, 0x6B, (byte)0x9C, 0x2D, 0x34, 0x02, 0x3A, 0x7C, 0x74, 0x58, (byte)0xD0, 0x68, 0x4C, 0x1D, (byte)0xD3, (byte)0x80, (byte)0xD0, (byte)0xF8, 0x49, 0x17, (byte)0x99, (byte)0xE3, (byte)0xB9, 0x25, (byte)0x8C, 0x44, (byte)0xFA, (byte)0xC4 }; String publicKey = publicKeyString; //公钥解出出AEK KEY IV String aeskey = new String(RSAUtils.publicKeyDecrypt(publicKey, keydata)); //前16字节是AES key, 后16字节是IV System.out.println("aeskey:"+aeskey); //解密后的值 fda958f6-07e5-47e4ae2f7b-96b5-4a7.3、AES解密出压缩后设备数据 复制代码 隐藏代码 /** * * @param FilePath 待解密的 deump 压缩后的设备数据 * home.php?mod=space&uid=155549 解密后的压缩数据 */ public static byte[] aesDecrypt(String FilePath, String key, String iv) { try { if (FilePath.isEmpty() || key.isEmpty()){ return null; } // 将字符串转为byte,返回解码后的byte[] byte[] encryptBytes = {}; encryptBytes = FileUtils.getContent(FilePath); // 创建密码器 KeyGenerator kgen = KeyGenerator.getInstance(EncryptAesUtil.AES); kgen.init(128); // 初始化为解密模式的密码器 Cipher cipher = Cipher.getInstance(ALGORITHMS); cipher.init(Cipher.DECRYPT_MODE, new SecretKeySpec(key.getBytes(), EncryptAesUtil.AES), new IvParameterSpec(iv.getBytes(StandardCharsets.UTF_8))); byte[] decryptBytes = cipher.doFinal(encryptBytes); String decstr = bytesToHex(decryptBytes); System.out.println("decryptBytes:"+decstr); return decryptBytes; } catch (Exception e) { System.out.println(e.getMessage() + e); } return null; } //前16字节是AES key, 后16字节是IV String key = "fda958f6-07e5-47"; String iv = "e4ae2f7b-96b5-4a"; //AES 解密压缩后设备数据 EncryptAesUtil.aesDecrypt("dump_deviceinfo_AES.data",key, iv);还有一层解密是VM中的,要还原大部分Handle,VM代码没有强混淆,分析起来还是比较容易的,这里就留一个坑吧,给有意愿深入搞搞的同学入坑。 |
【本文地址】
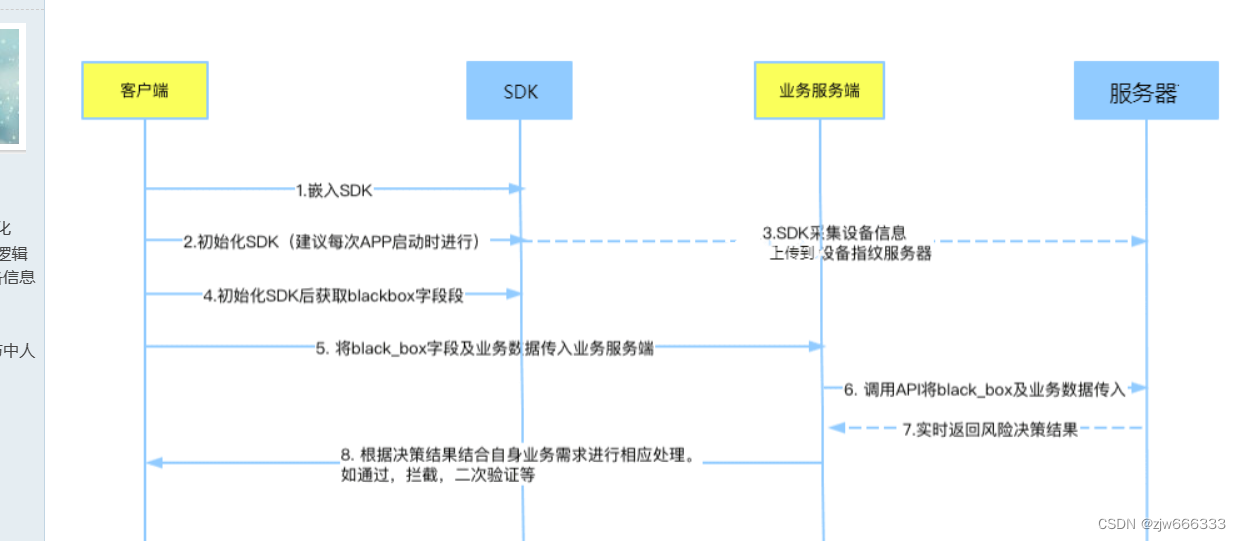
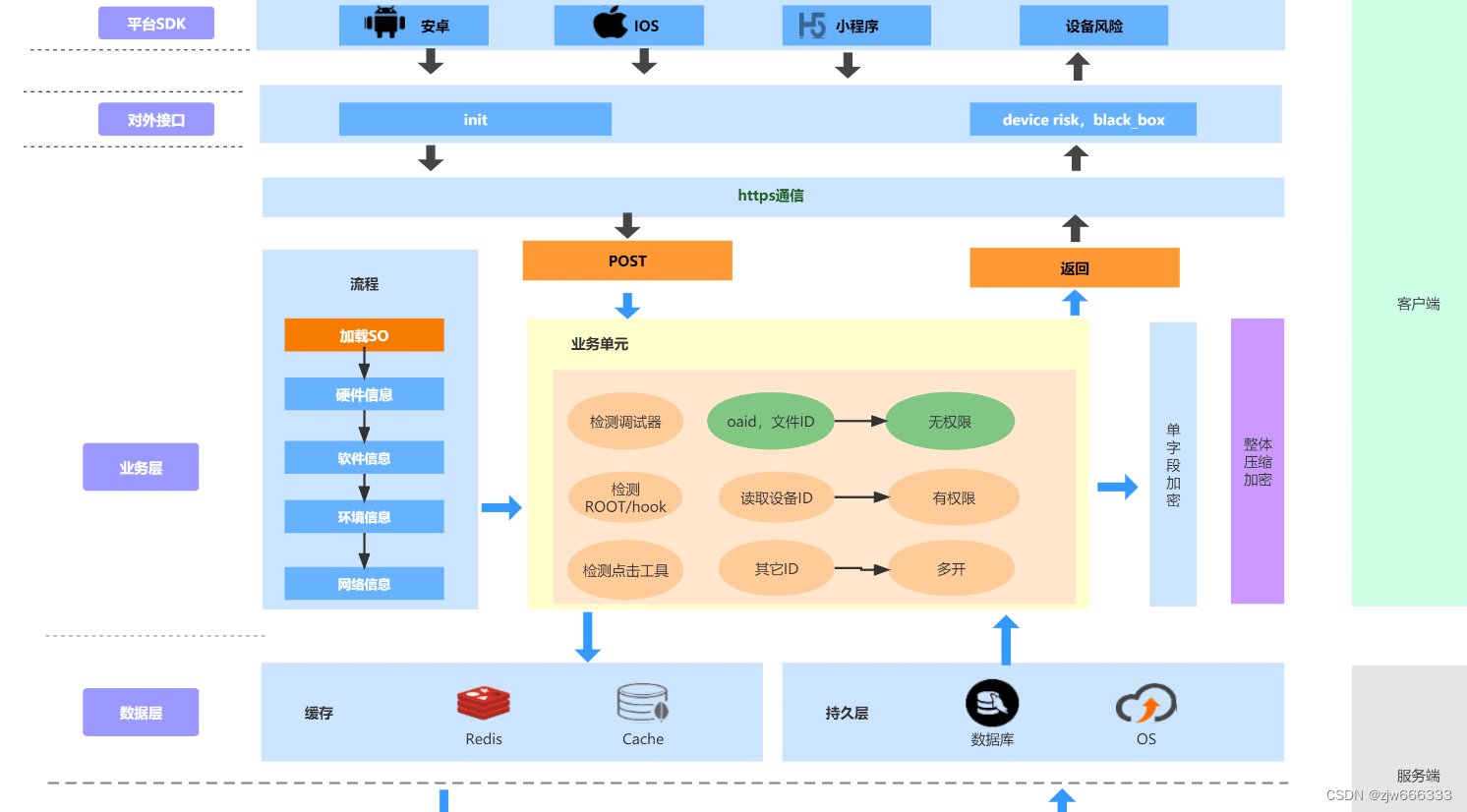 图2-3
图2-3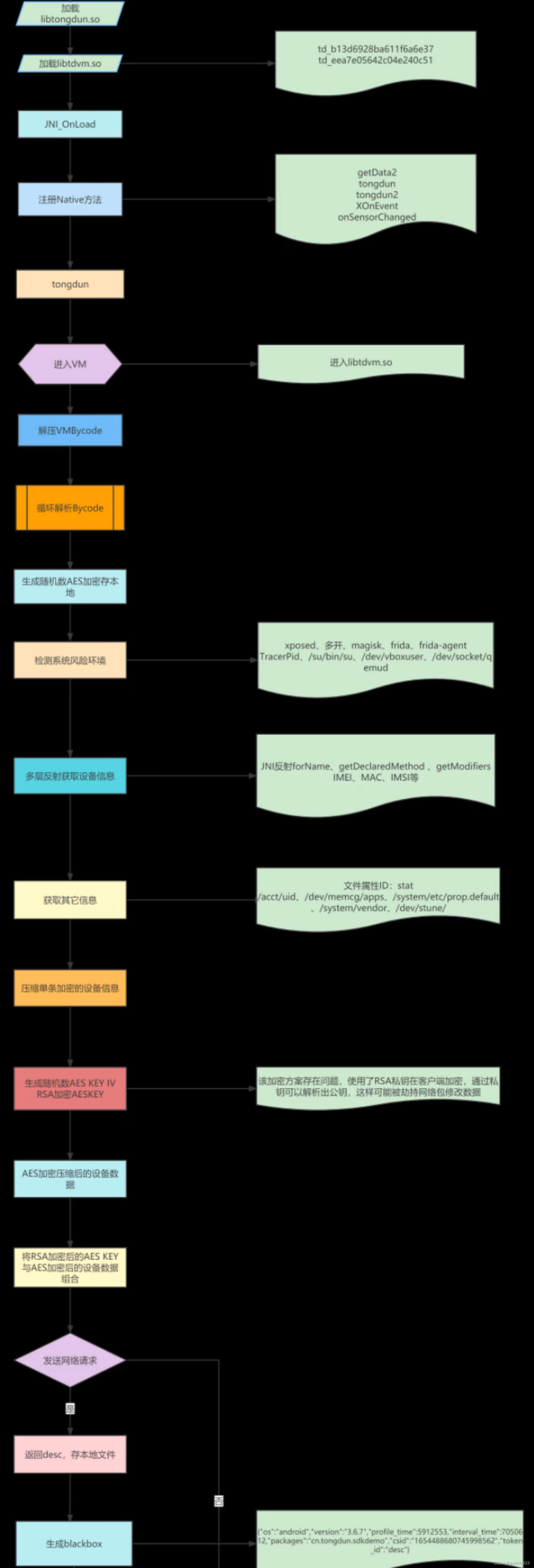 图3-4
图3-4