Linux下为普通用户添加root权限(常用) |
您所在的位置:网站首页 › rrot权限 › Linux下为普通用户添加root权限(常用) |
Linux下为普通用户添加root权限(常用)
|
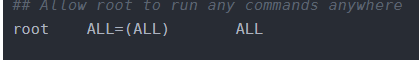
centos7 版本,我们不可能每次都用root账号登陆,root账号公认的不安全,所以一般都会创建一个专有权限的普通账号,下面创建一个具有root权限的普通账号。 [root@localhost ~]# groupadd test [root@localhost ~]# useradd -g test test [root@localhost ~]# passwd test 更改用户 test 的密码 。 新的 密码: 无效的密码: 过于简单化/系统化 无效的密码: 过于简单 重新输入新的 密码: passwd: 所有的身份验证令牌已经成功更新。创建完用户后,需要给用户添加权限。 [root@localhost ~]# chmod -v u+w /etc/sudoers mode of '/etc/sudoers' changed from 0440 (r--r-----) to 0640 (rw-r-----)修改sudoers权限,使其可编辑,编辑sudoers文件。 [root@localhost ~]# vim /etc/sudoers ## Sudoers allows particular users to run various commands as ## the root user, without needing the root password. ## ## Examples are provided at the bottom of the file for collections ## of related commands, which can then be delegated out to particular ## users or groups. ## ## This file must be edited with the 'visudo' command. ## Host Aliases ## Groups of machines. You may prefer to use hostnames (perhaps using ## wildcards for entire domains) or IP addresses instead. # Host_Alias FILESERVERS = fs1, fs2 # Host_Alias MAILSERVERS = smtp, smtp2 ## User Aliases ## These aren't often necessary, as you can use regular groups ## (ie, from files, LDAP, NIS, etc) in this file - just use %groupname ## rather than USERALIAS # User_Alias ADMINS = jsmith, mikem ## Command Aliases ## These are groups of related commands... ## Networking # Cmnd_Alias NETWORKING = /sbin/route, /sbin/ifconfig, /bin/ping, /sbin/dhclient, /usr/bin/net, /sbin/iptables, /usr/bin/rfcomm, /usr/bin/wvdial, /sbin/iwconfig, /sbin/mii-tool ## Installation and management of software # Cmnd_Alias SOFTWARE = /bin/rpm, /usr/bin/up2date, /usr/bin/yum ## Services # Cmnd_Alias SERVICES = /sbin/service, /sbin/chkconfig, /usr/bin/systemctl start, /usr/bin/systemctl stop, /usr/bin/systemctl reload, /usr/bin/systemctl restart, /usr/bin/systemctl status, /usr/bin/systemctl enable, /usr/bin/systemctl disable ## Updating the locate database # Cmnd_Alias LOCATE = /usr/bin/updatedb ## Storage # Cmnd_Alias STORAGE = /sbin/fdisk, /sbin/sfdisk, /sbin/parted, /sbin/partprobe, /bin/mount, /bin/umount ## Delegating permissions # Cmnd_Alias DELEGATING = /usr/sbin/visudo, /bin/chown, /bin/chmod, /bin/chgrp ## Processes # Cmnd_Alias PROCESSES = /bin/nice, /bin/kill, /usr/bin/kill, /usr/bin/killall ## Drivers # Cmnd_Alias DRIVERS = /sbin/modprobe # Defaults specification # # Refuse to run if unable to disable echo on the tty. # Defaults !visiblepw # # Preserving HOME has security implications since many programs # use it when searching for configuration files. Note that HOME # is already set when the the env_reset option is enabled, so # this option is only effective for configurations where either # env_reset is disabled or HOME is present in the env_keep list. # Defaults always_set_home Defaults match_group_by_gid # Prior to version 1.8.15, groups listed in sudoers that were not # found in the system group database were passed to the group # plugin, if any. Starting with 1.8.15, only groups of the form # %:group are resolved via the group plugin by default. # We enable always_query_group_plugin to restore old behavior. # Disable this option for new behavior. Defaults always_query_group_plugin Defaults env_reset Defaults env_keep = "COLORS DISPLAY HOSTNAME HISTSIZE KDEDIR LS_COLORS" Defaults env_keep += "MAIL PS1 PS2 QTDIR USERNAME LANG LC_ADDRESS LC_CTYPE" Defaults env_keep += "LC_COLLATE LC_IDENTIFICATION LC_MEASUREMENT LC_MESSAGES" Defaults env_keep += "LC_MONETARY LC_NAME LC_NUMERIC LC_PAPER LC_TELEPHONE" Defaults env_keep += "LC_TIME LC_ALL LANGUAGE LINGUAS _XKB_CHARSET XAUTHORITY" # # Adding HOME to env_keep may enable a user to run unrestricted # commands via sudo. # # Defaults env_keep += "HOME" Defaults secure_path = /sbin:/bin:/usr/sbin:/usr/bin ## Next comes the main part: which users can run what software on ## which machines (the sudoers file can be shared between multiple ## systems). ## Syntax: ## ## user MACHINE=COMMANDS ## ## The COMMANDS section may have other options added to it. ## ## Allow root to run any commands anywhere root ALL=(ALL) ALL ## Allows members of the 'sys' group to run networking, software, ## service management apps and more. # %sys ALL = NETWORKING, SOFTWARE, SERVICES, STORAGE, DELEGATING, PROCESSES, LOCATE, DRIVERS ## Allows people in group wheel to run all commands %wheel ALL=(ALL) ALL ## Same thing without a password # %wheel ALL=(ALL) NOPASSWD: ALL ## Allows members of the users group to mount and unmount the ## cdrom as root # %users ALL=/sbin/mount /mnt/cdrom, /sbin/umount /mnt/cdrom ## Allows members of the users group to shutdown this system # %users localhost=/sbin/shutdown -h now ## Read drop-in files from /etc/sudoers.d (the # here does not mean a comment) #includedir /etc/sudoers.d在 注意: test ALL=(ALL) NOPASSWD:ALL可以将第二组修改为NOPASSWD:ALL,这样使用sudo的时候就不用输入密码了。 将sudoers文件权限修改为不可编辑 [root@localhost ~]# chmod -v u-w /etc/sudoers mode of "/etc/sudoers" changed from 0640 (rw-r-----) to 0440 (r--r-----)此时,具有root权限的用户test就操作完了。
可能出现问题: 1、使用test用户进行切换(su root)root用户,提示鉴定故障。 可能在权限不足带来的问题。 检查办法如下: 1)检查/etc目录下passwd的权限,该文件应该具备的权限如下: [root@localhost ~]# ll /etc/passwd -rw-r--r--. 1 root root 2347 4f 16 21:00 /etc/passwd如果该权限不足,则使用chmod 补充完成。 2)检查/bin/su文件是否有s位权限 也有可能是所属用户为普通用户,该文件应该具备的权限如下: [root@localhost ~]# ll /bin/su -rwsrwxrwx. 1 root root 32128 8f 9 2019 /bin/su如果该权限不足,则使用chmod u+s /bin/su补充完成即可。 |
【本文地址】
 下面添加同样的一样。
下面添加同样的一样。